Hi everyone
Today we are going to look for a Box called Sea which is rated as Intermediate in terms of difficulty. This machine has various phases: Recon, Enumeration, Exploitation and Privilege Escalation.
Box Type: Linux
Recon & Enumeration
Enumeration plays a very significant role in pen testing. The more properly you enumerate the more it will be easy to get a foothold on the target.
First, we will check whether target is reachable or not with ping command:
ping Target_IP
With ping command output we found that the target is reachable.
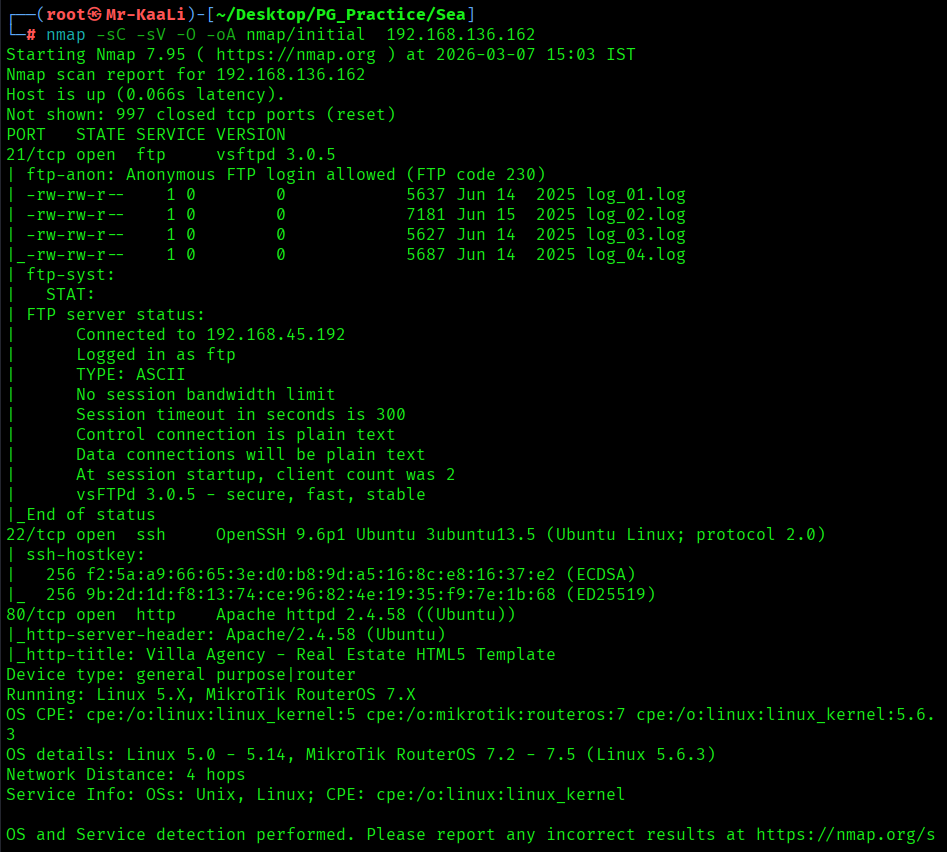
Now let’s move ahead and run the port scan for which we will be using Nmap a popular tool for port scanning and it will provide details of the various ports which are in Open state. The command for that will be:
nmap -sC -sV -O -oA nmap/initial 192.168.136.162
nmap -sC -sV -O -p- -oA nmap/full 192.168.136.162 -T4
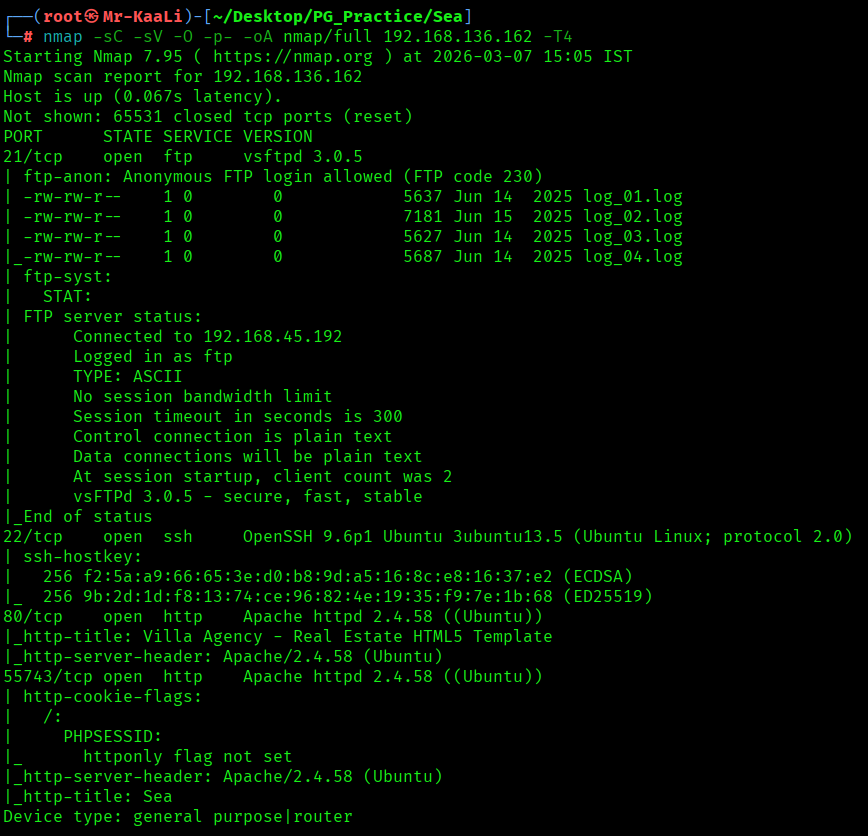
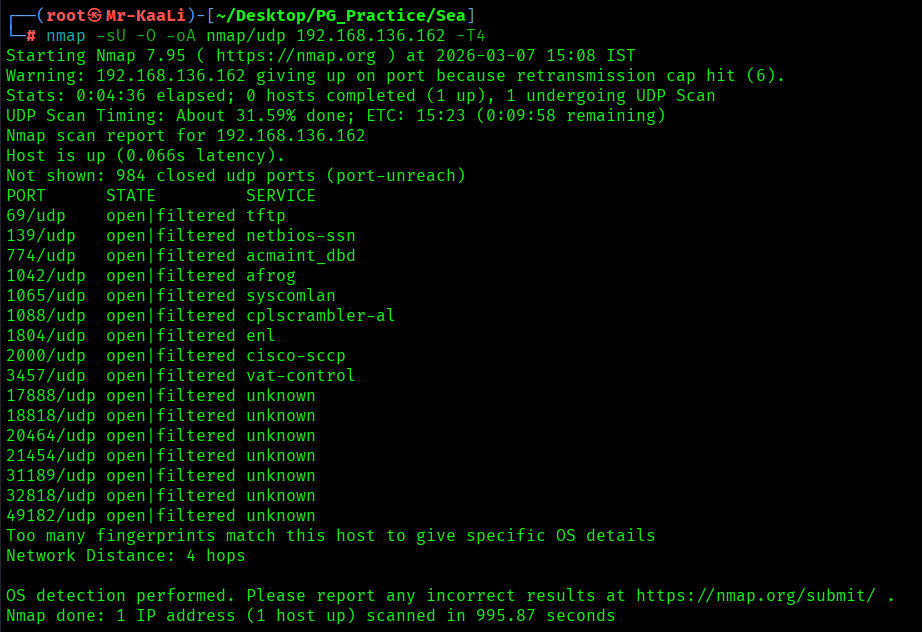
Now let’s also execute the full scan and UDP Scan:
I discovered these ports are open:
- 21/tcp – FTP Service running VSFTPD 3.0.5
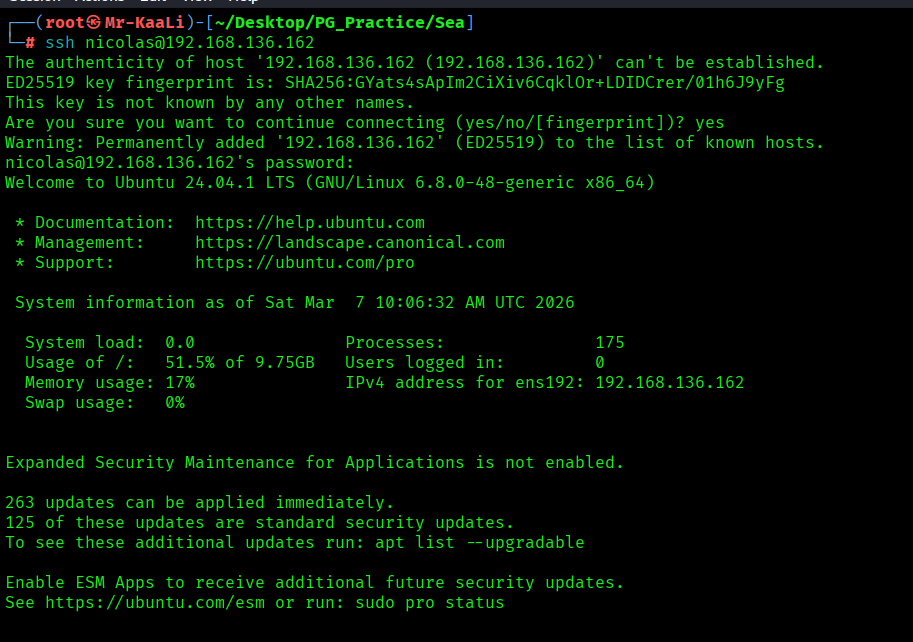
- 22/tcp – SSH Service running OpenSSH 9.6p1 Ubuntu 3ubuntu13.5 (Ubuntu Linux; protocol 2.0)
- 80/tcp – HTTP Service running Apache httpd 2.4.58 ((Ubuntu))
- OS: Linux
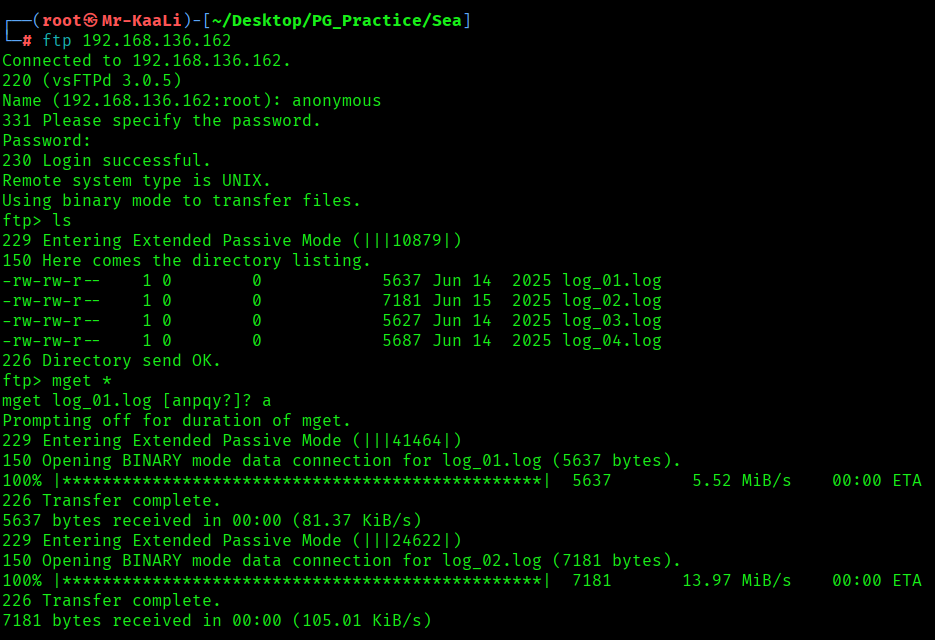
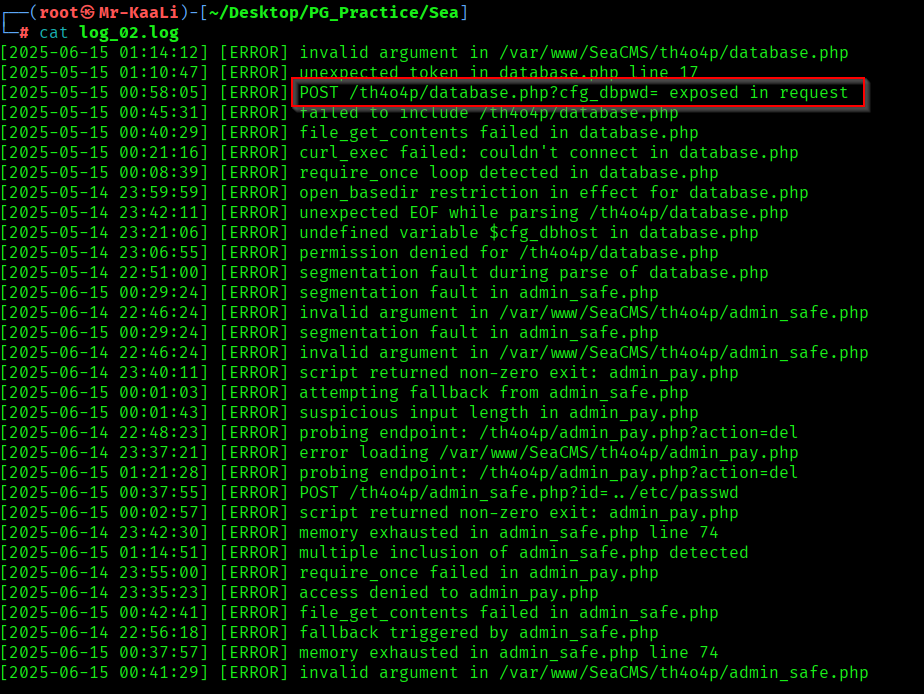
Let’s move ahead and check the anonymous ftp running:

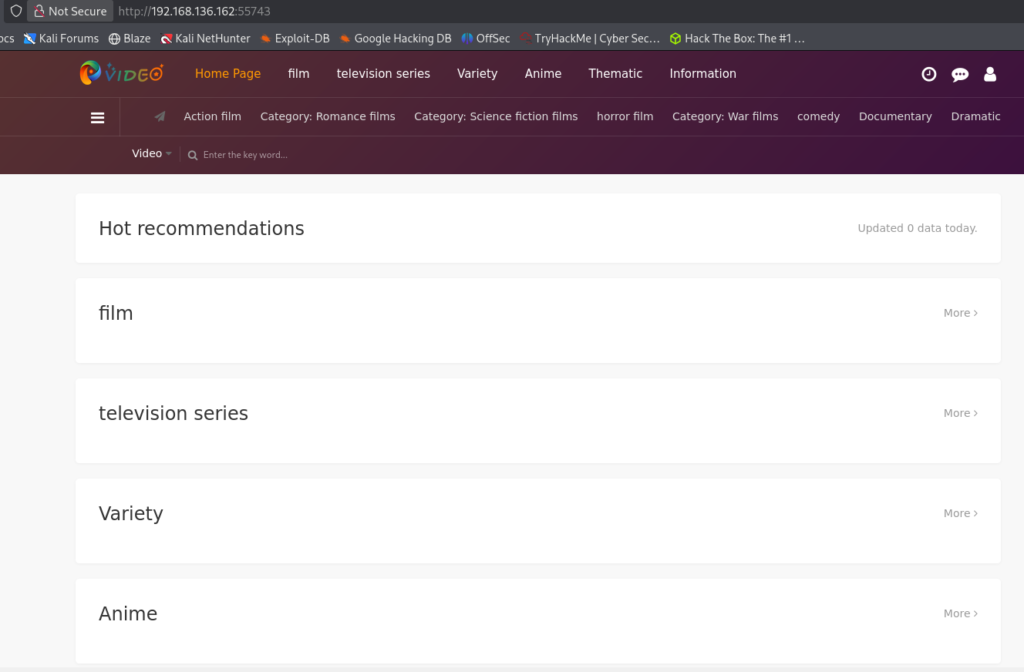
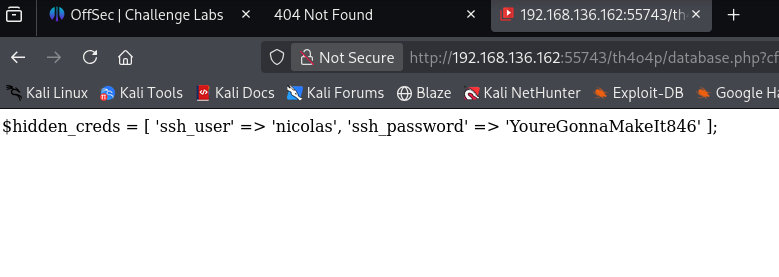
Let’s move ahead and check the IP in the web browser and I found page on port 55473:
Exploitation
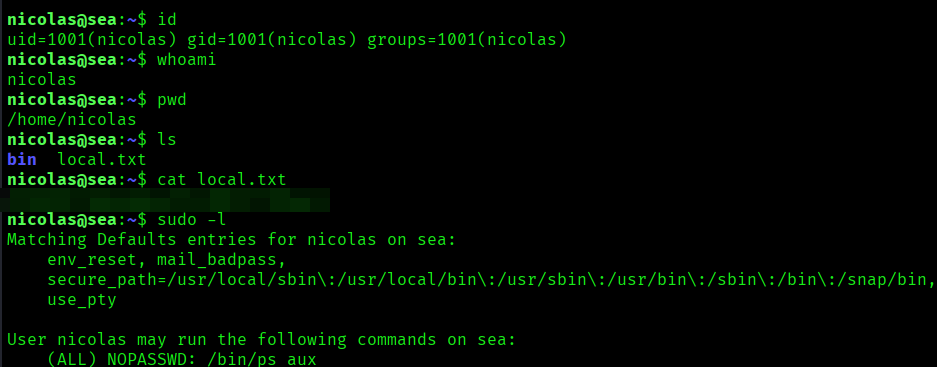
Privilege Escalation


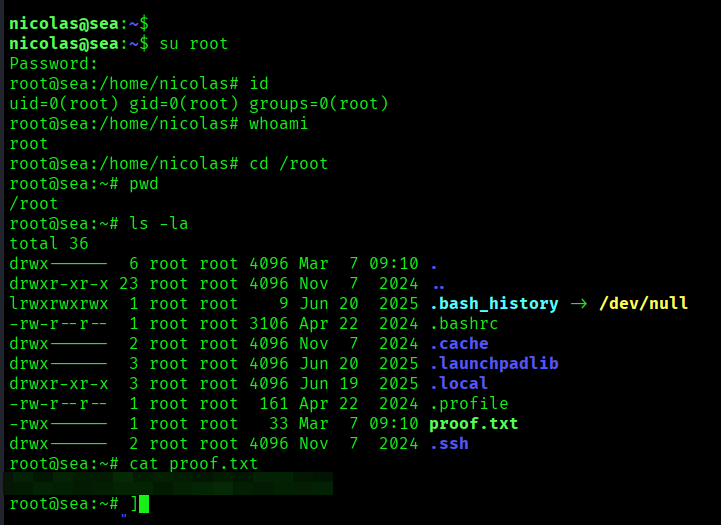
The above image shows the proof.txt file.
Key Takeaways
- Identify the web stack — CMS/framework details may reveal exploits.
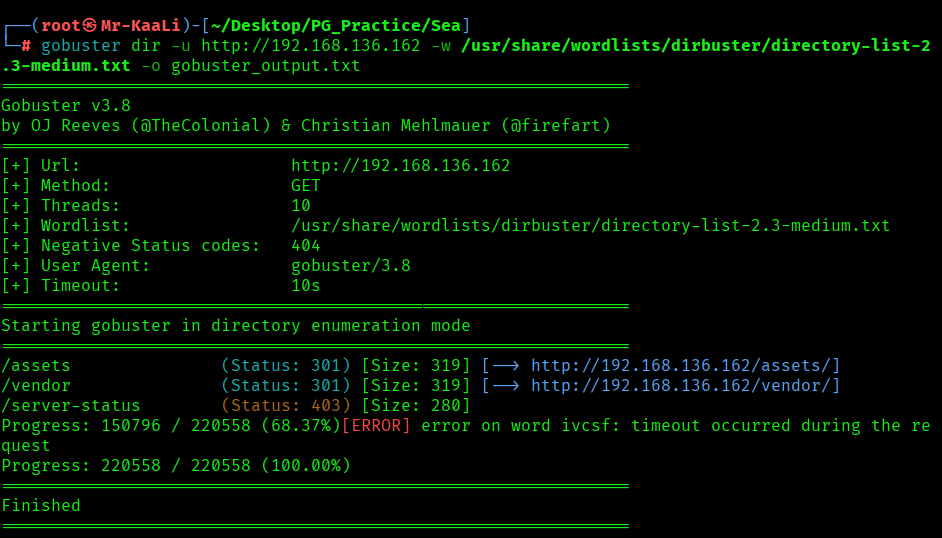
- Enumerate directories — hidden paths can expose entry points.
- Check for weak credentials — configs or backups may leak logins.
- Exploit web functionality — inputs or uploads may allow RCE.
- Enumerate post-exploitation — review files, cron jobs, and permissions.
- Search for plaintext credentials — logs or configs may lead to root.
If you enjoyed this post, share it with your friends and colleagues!